By 2026, one of the most persistent challenges in digital payments remains frustratingly simple: cards change, but merchants don’t know it until a payment fails. Every time a bank reissues a card for expiry, portfolio migration, fraud replacement or BIN restructuring millions of stored credentials silently break. These failures generate false declines, lost renewals, stalled subscriptions and involuntary churn that merchants neither expect nor control. In high-risk verticals, where issuer risk models are particularly sensitive, this disruption is even more pronounced.
Token Lifecycle Management (TLM) is the first infrastructure-level solution that meaningfully addresses this problem. Instead of stored PANs going stale, network tokens issued through Visa Token Service (VTS) and Mastercard MDES are refreshed automatically whenever the underlying card changes. This means the merchant continues charging the same token, while the customer’s updated card details propagate behind the scenes no customer action, no re-entry, no friction.
This shift matters because approval performance in 2026 is no longer shaped only by strong authentication or optimised routing. It is shaped by credential continuity the ability of a stored payment method to survive issuer changes without collapsing into a decline. The more merchants rely on recurring revenue, stored credentials, digital wallets or subscription billing, the more lifecycle stability becomes a performance driver rather than a back-office detail.
At the same time, regulatory tightening under PCI DSS v4.0 and the EU’s emerging PSD3/PSR package is pushing merchants to reduce PAN exposure and adopt secure, network-managed credentials. Tokenisation alone reduces PCI scope, but tokenisation with lifecycle management directly improves approval consistency, SCA outcomes and issuer trust.
Across high-risk segments, gaming, FX, e-commerce, SaaS, digital goods, wallets and cross-border services, merchants are already reporting measurable gains. Higher retry recovery, lower involuntary churn, fewer “expired card” declines and a more predictable authentication pattern all point to the same conclusion: lifecycle-managed tokens are no longer a technical enhancement. They have become a commercial engine.
In this blog, we break down how Token Lifecycle Management works, why issuers favour it, how it changes approval behaviour, and how high-risk merchants are using it to build more stable, more resilient revenue in 2026.
- From PAN Expiry Chaos to Token Continuity
- How Token Lifecycle Management Actually Works
- Why Stored Credentials Break: The Hidden Root Causes (2024–2026)
- Approval Stability: How Lifecycle Updates Reduce False Declines
- Retention Impact: Reducing Involuntary Churn in Subscriptions, SaaS & Wallets
- Multi-Acquirer Routing: Why Lifecycle Management Matters Even More Under Orchestration
- Retry Logic: How Tokenised Retries Recover Revenue PAN-Based Retries Lose
- High-Risk Corridor Lens: LATAM, APAC & Europe
- Fraud, SCA & Token Behaviour: Why Lifecycle Updates Improve Authentication Outcomes
- KPI Framework: Measuring Lifecycle Performance in 2026
- Implementation Roadmap: Deploying Lifecycle Management in Practice
- Phase 1: Enable Network Tokens & Token Requestor (TR) Capabilities
- Phase 2: Migrate Existing Stored Credentials to Network Tokens
- Phase 3: Connect Lifecycle Update Events to Merchant Systems
- Phase 4: Update Routing Logic, Retries & Billing Cadence
- Phase 5: Validate SCA, Fraud & Authentication Behaviour
- Phase 6: Monitor Lifecycle KPIs & Close Operational Gaps
- 2026 Strategy: Designing a Token-First Retention Engine
- Conclusion
- FAQs
From PAN Expiry Chaos to Token Continuity
For more than a decade, merchants have relied on stored PANs and account updater services to maintain recurring billing and stored-credential flows. But as digital commerce expanded and banks accelerated card reissuance cycles, this infrastructure began to show structural weaknesses. Customers rarely notice when their bank replaces a card, but merchants feel the impact immediately: subscription renewals fail, wallet top-ups break, and high-frequency services lose customers who never intended to leave.
The PAN fragility problem
A PAN is a static credential. Once a bank reissues a card due to expiry, portfolio migration, fraud, or operational refresh the PAN stored by the merchant becomes outdated. Even with encrypted vaulting and PCI-compliant handling, the stored number is still tied to a credential that no longer exists. The result is a decline that reveals nothing to the merchant about the underlying cause. “Do Not Honour,” “Expired Card,” “Restricted Card”, and similar codes mask the real issue: the bank has issued a new card, but the merchant is still billing the old one.
Why account updater never fully solved this issue
For years, acquirers and schemes attempted to soften the impact by offering account updater services. These helped, but with limitations:
- Updates were not always real-time,
- Cross-border portfolios were inconsistent
- Issuers had different participation levels
- Reissue triggers (like fraud replacement) rarely sync with updater timing.
This lag meant that subscription-heavy merchants continued to experience unnecessary failures, even though the customer relationship remained intact.
How token continuity changes the architecture
Network tokenisation introduces a new model: the token itself survives reissuance. When a customer’s card changes, the issuer updates the underlying account behind the token, not the token the merchant stores. Instead of a brittle, static PAN, the merchant holds a persistent credential that behaves like a long-lived identity key. Transactions continue without interruption because the token remains valid even when the PAN it represents has already been retired.
From unpredictable declines to predictable continuity
The practical difference is significant. PAN-based billing forces merchants to react to failures they can’t anticipate. Token lifecycle management reverses that dynamic by eliminating the failure point. The merchant no longer needs to detect what changed, initiate outreach or prompt the customer to update their details. The system simply continues to bill successfully, because the credential has been refreshed quietly in the background.
By 2026, this continuity has become one of the strongest drivers of approval stability. Merchants have learned that the greatest threat to recurring revenue is not customer intent it’s infrastructure fragility. Token lifecycle management replaces that fragility with a durable, network-managed identity that keeps billing intact even when cards change. It’s the structural foundation that turns tokenisation from a compliance tool into a true performance engine.
How Token Lifecycle Management Actually Works
Token Lifecycle Management (TLM) sits inside the card networks not inside the merchant, not inside the PSP, and not inside the gateway. This is what makes it powerful. Instead of relying on merchants to refresh stored credentials or on acquirers to batch-update vaults, the networks themselves maintain the relationship between the token and the underlying card. When the PAN changes, the token remains stable. When the issuer reissues a card, the token updates automatically. When a portfolio moves to a new BIN range, the token’s mapping adjusts instantly.
To understand why this matters in 2026, it helps to break down how lifecycle events propagate across the ecosystem.
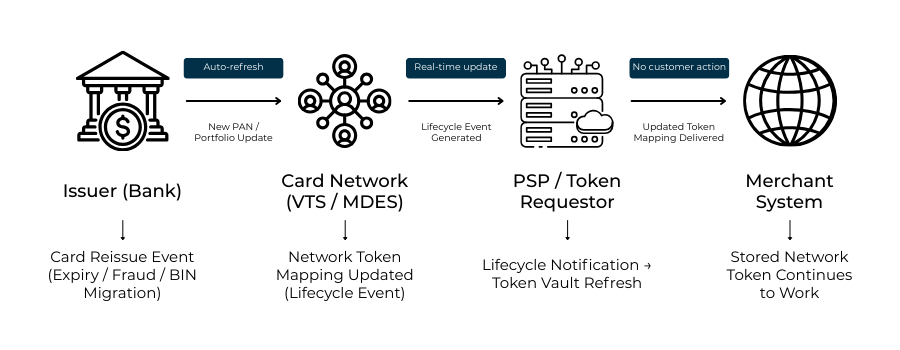
The Token Lifecycle Update Flow (Visa VTS & Mastercard MDES)
A lifecycle update begins at the issuer, not at the merchant. When a bank reissues a card for expiry, fraud replacement, BIN migration or operational refresh it pushes the new credential data to the card network. At that moment, Visa Token Service (VTS) or Mastercard MDES checks whether a network token exists for that card.
If a token is present, the network updates the token mapping automatically, linking the token ID to the new card details.
From here, the token update flows outward:
- The network token vault is refreshed
The token continues to represent the same “identity,” but now points to an updated funding account. - The PSP/token requestor is notified
PSPs who act as token requestors (TRs) receive lifecycle update events via secure channels. These events update the token metadata inside the PSP’s own vault. - The merchant’s stored credentials remain unchanged
The merchant continues to store the same token they stored before; nothing breaks. There is no need to prompt the customer to update payment details. - Future transactions use refreshed credentials automatically
When the merchant charges the token again, the issuer sees the new, updated credential not the expired or replaced PAN.
This means the entire refresh process occurs without any merchant involvement. It is invisible, continuous and instantaneous.
Why lifecycle management is fundamentally different from account updater
Account updater depended on acquirer participation, batch processes and issuer opt-in. Lifecycle management does not. It is part of the network-level infrastructure.
Where the account updater tried to “patch” the problem, lifecycle management removes the problem entirely by making the token the primary credential, not the PAN.
The result is a structural shift in how stored credentials behave:
- All tokens stay alive even when cards don’t, and
- All tokens continue to function across every PSP, route and acquirer.
This distinction is what makes lifecycle management the foundation of stable recurring revenue in 2026.
Why this matters for high-risk merchants
Merchants in gaming, FX, digital goods, subscription SaaS and cross-border commerce face a disproportionate volume of card reissuance. Fraud pressure is higher, issuer scrutiny is tighter and card portfolios change more frequently. Lifecycle-managed tokens remove this fragility. A customer can have a card replaced three times in 12 months, but the merchant will never feel any of those shocks the token keeps billing.
By 2026, Token Lifecycle Management will have become one of the most important components of every serious payment stack. It is not only a compliance mechanism or a way to minimise PCI scope; it is a performance infrastructure that protects revenue by keeping credentials alive long after the underlying cards have changed.
Why Stored Credentials Break: The Hidden Root Causes (2024–2026)
For years, merchants assumed that payment failures in subscription and stored-credential flows were caused by customer behaviour, insufficient balance, card misuse or deliberate cancellation. But by 2026, data across acquirers, PSPs and high-risk verticals shows a different story. Most declines are not behavioural at all. They stem from structural weaknesses in the underlying credential model. Understanding these root causes explains why Token Lifecycle Management has become essential rather than optional.
Card reissuance: the silent disruptor
One of the largest sources of payment failure is also the least visible. When banks reissue cards through expiry, fraud replacement, BIN migrations or portfolio upgrades, they seldom inform merchants. The customer continues using the service normally, unaware that the stored credential no longer matches the account behind it. When the next renewal attempt hits, the merchant receives a generic decline, often without any useful signal. The relationship between merchant and customer is intact; the relationship between merchant and card is not.
Risk-model resets and issuer-level tightening
Another driver of unexpected declines is issuer behaviour itself. Risk models are frequently recalibrated, especially in high-risk corridors and digital-first portfolios. A card that authenticated smoothly yesterday may trigger additional friction today simply because the issuer updated its fraud thresholds or authentication patterns. PAN-based credentials amplify this volatility because issuers see them as static and easily misused. When the PAN appears through a new device, channel or acquirer, issuer suspicion increases even if the customer is legitimate.
Cross-border frictions and corridor inconsistencies
Merchants operating across multiple regions experience additional instability. A PAN routed through a domestic acquirer may be treated leniently, while the same PAN routed through a cross-border corridor may trigger elevated checks. Stored credentials break more frequently in regions with tighter risk controls, faster portfolio turnover or stronger issuer fraud mandates. Card networks recognise this inconsistency, which is one reason lifecycle-managed tokens were designed to behave predictably across corridors.
Why do these failures accumulate into churn?
Individually, each failure looks like a simple decline. Collectively, they form the backbone of involuntary churn revenue lost, not because customers choose to leave but because payments fail without warning. Studies across subscription-heavy verticals show that involuntary churn can represent a quarter or more of total churn, particularly in markets where issuer behaviour is volatile. This is why lifecycle continuity matters: it removes structural fragility that PAN storage has never been able to overcome.
By 2026, the industry will increasingly recognise that payment failures are rarely the customer’s fault. They are failures of identity consistency, mismatches between what merchants store and what issuers expect. Token Lifecycle Management replaces this mismatch with continuity, ensuring payments continue even as the underlying ecosystem shifts around them.
Approval Stability: How Lifecycle Updates Reduce False Declines
Approval performance in 2026 is shaped less by front-end optimisation and more by the stability of the underlying credential. Issuers make risk decisions on the basis of identity continuity: whether the credential being presented behaves like the same customer, on the same device, using the same payment method that the issuer trusts. When a stored PAN becomes stale, that continuity collapses. Token Lifecycle Management (TLM) restores it.
The issuer’s point of view: trust depends on consistency
Behind every authorisation is a risk engine evaluating dozens of behavioural, device-level and credential-level signals. When a payment is made with a PAN that no longer matches the issuer’s current record, the issuer sees a mismatch: an old credential attempting a new transaction. Even if the customer is legitimate, this discrepancy triggers friction. Issuers will often downgrade confidence, demand additional SCA, or apply stricter fraud rules. The outcome: unnecessary declines.
Lifecycle-managed tokens change this dynamic. Because network tokens update automatically when a card changes, the issuer sees a current credential every time the merchant submits a charge. Instead of matching an outdated PAN against a fresh account, the issuer sees a clean, validated identity that aligns with its internal records. The result is a lower risk score and a higher probability of approval.
Reducing decline types that PANs frequently trigger
Most declines merchants receive offer limited insight: “Do Not Honour,” “Expired Card,” “Restricted Card,” or “Generic Decline.” In many cases, these codes mask card lifecycle issues. By removing stale credentials from the equation, TLM directly reduces the base rate of these declines. Issuers no longer have to choose between approving a transaction tied to an outdated credential or rejecting it out of caution; the token gives them a trusted, current reference point.
Stability across PSPs, acquirers and routes
The performance uplift becomes even clearer in multi-acquirer environments. When a merchant routes traffic across different PSPs or fallback paths, PAN-based transactions can behave inconsistently, especially if the issuer sees the same PAN appear through new or unfamiliar routes. Tokenised credentials reduce this volatility. Because the network token acts as the identity anchor, it behaves consistently regardless of route, corridor or acquirer. This stability is one of the main reasons orchestration platforms have begun prioritising tokenised credential flows as a first-class input.
Why lifecycle updates outperform account updater in approval recovery
Account updater attempted to solve the expiry problem, but it relied on batch processing and uneven issuer participation. It also applied only to certain types of reissuance. Token lifecycle updates, by contrast, originate at the issuer and update the token immediately. This real-time refresh dramatically improves the success of subsequent attempts, enabling merchants to avoid the “blind spots” that occur when PAN-based credentials silently go stale.
The result: predictable, resilient approval curves
Merchants that deploy TLM report not only higher approvals, but more importantly, stable approvals. Instead of fluctuations caused by reissuance cycles, portfolio changes or BIN migrations, approval rates begin to smooth out. For subscription-heavy models, SaaS, gaming, streaming, education, and mobility services that stability becomes a competitive differentiator. Approval stability also translates directly into lower involuntary churn and cleaner retry performance downstream.
Lifecycle management, therefore, represents more than a technical enhancement. It is one of the few interventions that aligns merchant expectations with issuer confidence, improving performance without increasing friction. In 2026, this alignment has become the foundation of predictable, high-quality authorisations.
Retention Impact: Reducing Involuntary Churn in Subscriptions, SaaS & Wallets
In subscription and high-frequency payment models, retention depends on something deceptively simple: the customer must be able to pay. When the stored credential breaks, the subscription breaks with it regardless of how satisfied the user is. This is the core challenge Token Lifecycle Management solves. It stabilises the credential that underpins recurring revenue, turning what used to be a major source of churn into a point of continuity.
Where involuntary churn really comes from
The majority of churn in subscription and SaaS portfolios is not intentional. Customers do not typically cancel because they changed their mind; they cancel because their payment failed and they never returned. The root cause is nearly always the same: the card on file has been replaced or updated, and the merchant continues attempting charges against a credential that no longer exists. The user still wants the service. The payment method, however, no longer works.
This creates a pattern merchants know well: a sudden dip in renewals, a rise in “reactivation” attempts, and an increase in outbound reminders asking customers to update their payment details. Much of this manual recovery is unnecessary in a token-first model.
Scenario: Subscription SaaS merchant without lifecycle updates
- A customer’s card is reissued due to fraud.
- They continue using the SaaS product normally.
- The stored PAN expires silently.
- The next renewal attempt fails with a generic decline.
- The system sends two reminder emails; the customer sees them late or ignores them.
- The subscription lapses.
- The merchant loses a paying user not because of dissatisfaction, but because the credential expired.
Across SaaS and streaming businesses, this scenario repeats itself millions of times each year.
Scenario: Subscription SaaS merchant with lifecycle-managed tokens
- The customer’s card is reissued, but this time, the issuer updates the token mapping behind the scenes.
- The merchant continues billing the same token they have always billed.
- No decline occurs.
- No outreach campaign is triggered.
- The subscription remains active.
- The customer relationship remains undisturbed.
What changed? Not the billing logic, the credential did.
Wallets and high-frequency use cases see even stronger effects
Wallet-based merchants (gaming, FX, digital goods, mobility, online entertainment) often rely on stored credentials for daily or weekly transactions. Here, tokens with lifecycle management do more than retain subscribers; they retain active usage. When tokens stay fresh, deposit flows don’t stall, wallet balances don’t freeze, and user activity doesn’t drop. A single expired PAN can interrupt a user’s entire flow; a lifecycle-updated token removes that friction completely.
Why lifecycle updates outperform traditional recovery methods
Merchants have tried many ways to “fix” involuntary churn: dunning strategies, grace periods, billing retries, multi-channel reminders, and routing changes. These help, but they all occur after a failure. Lifecycle management prevents the failure itself. By keeping the credential alive across card updates, it removes the need for recovery workflows altogether.
This shift from reacting to failures to preventing them is what makes lifecycle management so powerful for retention. It stabilises recurring revenue at the credential level, ensuring that customer intent translates into continued usage without interruption.
Multi-Acquirer Routing: Why Lifecycle Management Matters Even More Under Orchestration
Merchants operating with orchestration platforms rely on multi-acquirer routing to stabilise approval rates, reduce processing costs and minimise exposure to issuer behaviour in any single corridor. But multi-acquirer setups introduce their own complexity: the same stored credential must behave consistently no matter where it is routed. This is precisely where lifecycle-managed tokens become critical.
The orchestration challenge: one customer, many routes
When a PSP or orchestration layer determines the best acquirer path for a transaction, it evaluates dozens of variables: corridor performance, issuer behaviour, risk signals, FX, latency and fallback availability. But the quality of the credential being routed often determines whether the optimisation works. A stale PAN routed across five acquirers is still a stale PAN. Routing can’t fix the underlying credential’s fragility.
Lifecycle-managed tokens change this equation. Because the token is continuously updated by the networks, it behaves predictably across every route. Whether the transaction flows through a domestic acquirer, a cross-border processor or a specialist high-risk PSP, the credential itself remains stable. This consistency gives orchestration platforms a reliable foundation to build their optimisation models on.
How lifecycle events propagate across multiple acquirers
When a lifecycle update occurs for example, when a card is replaced, the card networks refresh the token mapping instantly. The PSP or token requestor receives this update and pushes it into the merchant’s vault. From that moment, every acquirer in the merchant’s routing catalogue uses the same, updated credential without requiring synchronisation or coordination between them.
This uniformity is especially valuable in high-risk sectors, where acquirer availability fluctuates and fallback routing is common. Tokens ensure every route draws from the same current credential, eliminating the inconsistency that often appears when PAN-based credentials travel through diverse pathways.
Why orchestration “magnifies” the value of lifecycle tokens
In a single-acquirer setup, lifecycle management prevents isolated failures. In a multi-acquirer environment, it prevents systemic failures. Without lifecycle updates, each acquirer would attempt authorisations with an outdated PAN, producing multiple failures across multiple routes. Orchestration amplifies the failure. With lifecycle updates in place, orchestration instead amplifies the continuity every route benefits from the same refreshed token.
This is why, by 2026, leading orchestration platforms have begun treating lifecycle tokens as a primary signal. They offer cleaner retry logic, higher soft-decline recovery and smoother SCA behaviour across acquirers. Tokens provide the consistency that orchestration requires to deliver high approval performance in complex, multi-market payment stacks.
The performance outcome: fewer blind spots, smoother fallback
When routing logic fails and fallback paths activate, PAN-based transactions are vulnerable to entire chains of declines. But when lifecycle-managed tokens underpin the flow, fallback behaves predictably. Every acquirer in the sequence receives a valid, stable credential aligned with the issuer’s most recent record.
This dramatically increases the reliability of multi-acquirer routing, reducing avoidable declines and making orchestration both more resilient and more efficient. In 2026, lifecycle management has become one of the most important enablers of multi-acquirer success, not because it changes routing, but because it ensures routing has something stable to work with.
Retry Logic: How Tokenised Retries Recover Revenue PAN-Based Retries Lose
Retry logic has always been the last line of defence against revenue loss. When a payment fails, merchants rely on scheduled retries, adaptive retry windows or acquirer switching to recover the transaction. But retries built on PANs have a structural weakness: they retry the same outdated credential that caused the failure in the first place.
This is why retry recovery rates tail off sharply when a portfolio contains many stale stored cards. Each retry essentially replays an inevitable decline. The underlying credential is broken and no amount of timing optimisation can change that.
Token Lifecycle Management transforms retry performance because the credential being retried is not the one that failed. When a card is replaced or updated, the token mapping refreshes immediately. This means that even if the first attempt failed because the PAN was outdated, the second attempt may succeed because the token now reflects the new, updated credential behind the scenes.
This shift turns retries from reactive “attempts” into meaningful recovery events.
Mini Comparison Model: How PAN vs Token Retries Diverge
Scenario: A customer’s card is reissued due to fraud. Merchant attempts a monthly renewal.
Retry Using PAN
- Merchant retries the original PAN stored before reissue
- Issuer sees a credential that no longer matches the account
- Risk score spikes because the PAN is now invalid
- Decline repeats (even across different acquirers)
- Merchant must begin a dunning sequence
- Customer may never update details
- Revenue is lost even though the customer still wants the service
Retry Using a Lifecycle-Managed Token
- Issuer updates token mapping instantly when card changes
- Merchant retries the same token, but token now points to the new card
- Issuer sees a fresh, valid credential linked to the customer’s updated account
- Approval likelihood increases significantly
- No dunning required, no customer outreach, no interruption
- Renewal succeeds, subscription remains active
Why token-based retries outperform timing-based strategies
Traditional retry optimisation relied on timing models: waiting hours or days before trying again. But token-based retries operate on credential quality, not timing. Because the underlying mapping refreshes as soon as the card changes, the retry gains access to an updated, issuer-approved identity. Timing becomes secondary and the quality of the credential becomes the primary recovery driver.
This is why merchants using Token Lifecycle Management report higher first-retry recovery rates and more predictable retry curves. Tokens ensure the second attempt is materially different from the first, turning retries into a genuine revenue recovery mechanism rather than a procedural repetition.
High-Risk Corridor Lens: LATAM, APAC & Europe
Token Lifecycle Management behaves differently across regions, not because the technology changes, but because issuer risk behaviour, card-reissuance frequency and regulatory expectations vary widely. For high-risk merchants operating internationally, this makes lifecycle continuity especially valuable. Below is how the impact unfolds across three major corridors.
LATAM: High Reissuance, High Fraud, High Dependence on Stable Credentials
LATAM markets such as Brazil, Colombia, Chile and Mexico have historically shown some of the highest card-reissuance rates globally. Fraud-driven replacement cycles are frequent, BIN migrations are common, and issuers routinely refresh portfolios to meet evolving security standards. For subscription, gaming and digital goods merchants, this creates a persistently fragile stored-credential environment.
PAN-based renewals fail disproportionately in these markets because the underlying cards often change multiple times within a year. A subscription customer with an otherwise strong tenure may experience a silent failure simply because their bank issued a new card for a routine security update.
Lifecycle-managed tokens reduce this fragility by following the issuer’s changes instantly. The token remains stable across replacements, meaning Brazilian and Colombian issuers continue recognising the same customer identity even when the underlying number changes. This stability directly lowers “Do Not Honour” and “Expired Card” decline categories that are otherwise endemic to the region.
APAC: Regulation, Token Mandates and Rapid Portfolio Modernisation
APAC is where Token Lifecycle Management becomes not only valuable but sometimes unavoidable. Markets such as India have introduced strict card-data restrictions, effectively forcing merchants to rely on network tokens to store credentials. In India, lifecycle updates are not an optimisation, they are the only way for stored-credential commerce to function legally after the RBI prohibited merchant PAN storage. As issuers in India aggressively reissue cards for security compliance, network-managed lifecycle updates ensure that recurring charges continue without disruption.
Other APAC markets, including Singapore, Malaysia, Thailand and Indonesia, show rising issuer adoption of tokenisation frameworks aligned with VTS and MDES. With mobile-first portfolios and high digital penetration, issuers in these regions increasingly favour tokenised credentials because they enable cleaner SCA behaviour and device-linked identity signals. Lifecycle updates help maintain this consistency across both domestic and cross-border routes, reducing failures that originate from corridor-specific issuer rules.
Europe: PSD3, SCA & the Push for “Trusted Credentials”
Europe’s payments environment is shaped less by card reissuance and more by regulatory tightening, particularly around SCA and fraud accountability. Here, issuers prefer credentials that produce predictable, low-risk authentication patterns. Tokens with lifecycle management provide exactly that.
Under the EU’s upcoming PSD3/PSR framework, the Commission has signalled a renewed focus on secure, persistent customer authentication and improved fraud controls.
Lifecycle-managed tokens fit naturally into this environment. Because they maintain continuity across reissued cards, issuer risk engines encounter fewer sudden credential changes, one of the most common triggers for increased SCA friction or outright declines. Merchants operating in European high-risk verticals often see smoother, frictionless flows and more stable approval curves when lifecycle-managed tokens underpin their stored-credential logic.
Europe is also where orchestration-driven merchants benefit most: the consistent token identity supports multi-acquirer routing strategies across the region, eliminating decline spikes driven by corridor-specific issuer sensitivity.
Across all three corridors, the pattern is consistent: the more volatile the market, the more valuable token lifecycle continuity becomes. LATAM benefits from reduced reissuance-driven declines, APAC from regulatory alignment and issuer preference for secure credentials, and Europe from compliance coherence and improved authentication stability. For 2026 merchants, TLM acts as a harmoniser, smoothing out regional volatility and anchoring approval performance across borders.
Fraud, SCA & Token Behaviour: Why Lifecycle Updates Improve Authentication Outcomes
Strong Customer Authentication (SCA) was introduced to reduce fraud, but in practice, it often exposes the weaknesses of legacy credential models. When a PAN becomes outdated or behaves unpredictably, issuers respond by increasing friction: more challenges, more step-ups, more risk flags. For high-risk merchants, this creates a recurring pattern: transactions fail not because the customer is suspicious, but because the credential is.
Token Lifecycle Management changes this foundation. Instead of presenting issuers with a fragile, static PAN, the merchant presents a credential that evolves in lockstep with the customer’s real account. This synchronisation has a profound impact on both fraud scoring and authentication behaviour.
Stable credentials create stable risk profiles
Issuer risk engines operate on behavioural baselines. A credential that remains constant across devices, channels and reissuances appears lower risk. A PAN, however, becomes risky the moment the issuer updates it. To the issuer, an outdated PAN looks like a disconnected identity, a signal often correlated with counterfeit use, account takeover or third-party fraud.
Lifecycle-managed tokens eliminate this mismatch. Because the token remains current even when the underlying card changes, the issuer sees a continuous identity rather than a broken one. This reduces the likelihood of unexpected step-up challenges and prevents sudden drops into “high-risk” routing paths.
How lifecycle continuity improves 3DS2 flows
3DS2 authentication depends heavily on issuer confidence. When the issuer trusts the credential, the transaction can pass through frictionlessly. When the credential behaves unpredictably, issuers increase friction as a precaution.
Lifecycle-managed tokens influence this in three ways:
- Fewer “surprises” for issuer risk engines
The issuer does not encounter a PAN that it recently replaced. The credential aligns perfectly with its latest internal data. - Cleaner device and behavioural metadata
Tokens carry stable data fields and consistent identity signals, creating stronger matches during risk evaluation. - Lower likelihood of unnecessary SCA challenges
When identity continuity is preserved, issuers have fewer reasons to escalate to step-up authentication.
The result is a smoother authentication curve for both initial billing and recurring payments particularly in regulated markets where SCA rules are tightly enforced.
Fraud mitigation through token behaviour
Fraud models are heavily influenced by the credential lifecycle. Fraudsters rely on breakpoints moments when the card number changes, the customer updates details, or the system behaves inconsistently. Tokens remove many of these breakpoints by eliminating credential gaps.
For high-risk merchants, this produces several benefits:
- Fewer fraud-triggered declines due to mismatched credentials
- More predictable risk scoring for recurring billing
- Reduced false positives stemming from outdated PAN metadata
Stable tokens help issuers differentiate between legitimate customer activity and suspicious patterns with greater accuracy, ultimately lowering fraud exposure.
Why lifecycle-managed tokens outperform static secure credentials
Even traditional secure credentials, such as PANs stored in PCI-certified vaults cannot solve authentication volatility because they lack continuity. Their security properties may be strong, but their behavioural properties degrade the moment a card is reissued.
Lifecycle-managed tokens solve both sides of the problem:
- They are secure, because they avoid raw PAN storage and reduce PCI scope.
- They are consistent, because the underlying identity survives reissuances, fraud replacements and BIN migrations.
This dual benefit is what aligns token lifecycle management with the direction of PSD3 and SCA optimisation. The regulatory push for stronger authentication in the EU is increasingly pointing toward credentials that maintain identity stability rather than credentials that rely on static data.
Token Lifecycle Management is therefore not purely a security feature; it is a fraud, authentication and approval optimisation layer. By aligning merchant behaviour with issuer expectations, lifecycle-managed tokens remove the friction that has historically plagued high-risk verticals and recurring billing models. In 2026, this alignment has become a defining factor in whether merchants experience predictable approvals or persistent authentication volatility.
KPI Framework: Measuring Lifecycle Performance in 2026
Token Lifecycle Management only delivers its full value when merchants know how to measure it. In 2026, PSPs and high-risk merchants have begun treating lifecycle continuity as a standalone performance domain, with KPIs that sit alongside approval rate, SCA success and fraud ratio. These metrics reveal whether updated network tokens are truly improving stability, retention and revenue recovery.
1. Lifecycle Update Success Rate
This is the foundational lifecycle metric. It tracks how many network tokens were successfully refreshed following issuer-driven card changes. When a bank reissues or updates a card, the network issues a lifecycle event. A high success rate means that those events are flowing correctly through the PSP/token requestor and into the merchant’s vault. A dip in this metric often indicates gaps in integration, misconfigured token requestor settings or acquirer-level incompatibilities.
2. Token vs PAN Approval Uplift (Stored Credentials)
Merchants measure how approval rates differ when charging:
- Network tokens with active lifecycle updates, and
- Legacy PAN-based or non-updating vault tokens.
In high-risk sectors, the uplift is often most visible in recurring payments, cross-border corridors and wallets with high deposit frequency. Stable credentials deliver more predictable approvals, creating a smoother revenue curve.
3. Involuntary Churn Reduction Linked to Payment Failures
For SaaS, gaming, streaming, FX and digital wallets, involuntary churn is one of the most painful leakages in the revenue model. Lifecycle continuity reduces payment failures tied to expired or replaced cards. Tracking the delta before and after lifecycle adoption provides a direct quantification of retention impact.
4. Retry Recovery Rate (Tokenised Retries)
Tokens fundamentally change retry dynamics. With PANs, retries simply echo the same outdated credentials. With lifecycle-managed tokens, retries often succeed because the underlying account has already been updated.
Merchants track the proportion of recoverable failures that are successfully converted after the first retry. PSPs also track corridor-specific recovery patterns, where lifecycle updates may have an outsized impact (e.g., LATAM and India).
5. Cross-Acquirer Stability Index
In orchestration-heavy payment stacks, stored credentials travel across multiple acquirers.
This KPI measures how consistently a credential performs across routes. Lifecycle-managed tokens nearly always show lower variance between acquirers than PANs do, because issuer trust signals remain consistent across all routes.
6. Decline-Type Distribution Shift
A powerful diagnostic metric.
After adopting lifecycle tokens, merchants should see a measurable drop in lifecycle-related declines:
- Expired Card
- Invalid Account
- Do Not Honour (issuer behavioural catch-all)
Tracking the distribution over time reveals whether TLM is successfully mitigating the structural decline categories most related to card churn.
7. Cost Impact: Downstream Operational Load
Lifecycle updates reduce:
- Customer-service tickets
- Dunning workflow volume
- Reactivation campaign spend
- Billing-cycle delays.
Merchants evaluate these cost efficiencies alongside direct performance uplift, especially in subscription and wallet-driven verticals.
In 2026, PSPs and sophisticated merchants treat lifecycle KPIs as core operational levers. The shift away from PAN-based behaviour creates a more stable baseline for approvals, retries and SCA flows, and lifecycle performance becomes a measurable, optimisable discipline rather than an invisible back-end process.
The merchants who win in this environment are those who track lifecycle behaviour with the same rigour they apply to fraud models, routing logic and acquisition funnels.
Implementation Roadmap: Deploying Lifecycle Management in Practice
Token Lifecycle Management delivers its value only when it is implemented end-to-end across the PSP, orchestration layer, merchant vault, billing engine and retry logic. By 2026, merchants no longer treat tokenisation as a switch they “turn on.” Lifecycle continuity requires a coordinated rollout that touches multiple systems and data flows. The roadmap below reflects how leading high-risk merchants deploy TLM in real environments.
Phase 1: Enable Network Tokens & Token Requestor (TR) Capabilities
Every lifecycle update begins with the networks, so the first step is ensuring that the merchant’s PSP or orchestration provider is properly configured as a token requestor. In this phase, PSPs integrate directly with Visa Token Service (VTS) and Mastercard MDES, enabling the ability to create, store and refresh network tokens. For merchants, this phase is foundational: it establishes the credential format that will eventually replace PAN-based storage and sets the stage for lifecycle update flows.
Phase 2: Migrate Existing Stored Credentials to Network Tokens
Merchants typically hold thousands or millions of stored PANs, depending on their business model. Migration does not need to be abrupt; most PSPs support progressive tokenisation, where the next billing cycle or customer action triggers a token request. Over time, PANs are replaced with network tokens automatically. This gradual approach reduces operational risk while ensuring that lifecycle updates begin applying to an increasingly large share of the portfolio.
Phase 3: Connect Lifecycle Update Events to Merchant Systems
Once tokens begin flowing, lifecycle update events must be captured and propagated through merchant systems. This is where practical engineering begins. PSPs push update notifications, reflecting issuer-driven reissuance, portfolio changes or BIN migrations and the merchant vault must accept and map these events cleanly. Billing engines, subscription platforms, wallet systems and CRM tools must all operate with the updated token, ensuring continuity across every internal process that touches payments.
Phase 4: Update Routing Logic, Retries & Billing Cadence
Lifecycle updates only reach their full potential when orchestration layers and billing logic are aligned. Merchants adjust retry configurations so that retries use the updated token, not the failed PAN or outdated mapping.
This phase also includes verifying that multi-acquirer routing paths correctly use network tokens. When executed properly, fallback routes benefit from the same credential stability as primary routes, preserving approval performance even in complex payment stacks.
Phase 5: Validate SCA, Fraud & Authentication Behaviour
Lifecycle-managed tokens behave differently during SCA and risk evaluation. Merchants validate that their 3DS2 flows recognise the stable token identity and that authentication systems, whether issuer-driven or merchant-initiated, respond with fewer unnecessary step-ups. Fraud teams monitor behavioural patterns to confirm that lifecycle continuity removes false positives without reducing fraud controls.
Phase 6: Monitor Lifecycle KPIs & Close Operational Gaps
With TLM in production, merchants begin tracking lifecycle KPIs: update success rate, token–PAN approval uplift, reduction in lifecycle-related declines, retry recovery and involuntary churn deltas.This final phase transforms lifecycle management from a one-time integration into an ongoing optimisation discipline. PSPs and merchants use KPI feedback loops to refine routing logic, adjust billing windows and identify acquirers that underperform with tokenised credentials.
2026 Strategy: Designing a Token-First Retention Engine
By 2026, merchants who treat tokenisation as a compliance exercise are already falling behind. The shift toward Token Lifecycle Management has reframed the conversation: stable credentials are not a security upgrade, they are a revenue system. Merchants that understand this design their payment infrastructure around continuity, not correction. The goal is simple but transformative: prevent failures before they occur, rather than repairing them after the fact.
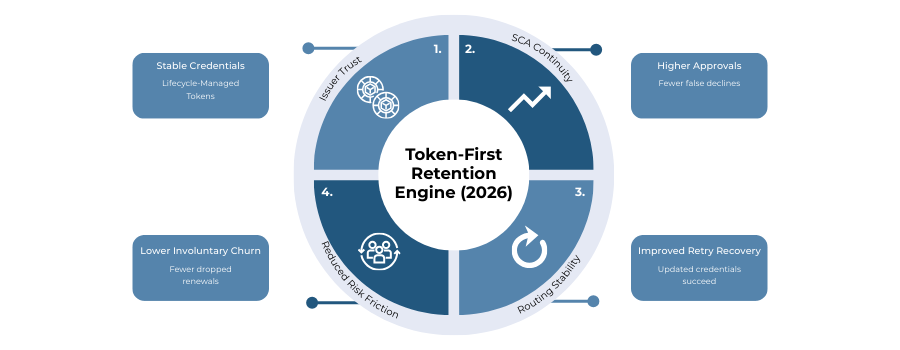
From billing resilience to commercial strategy
A token-first retention engine begins with acknowledging that a subscription, wallet balance, or stored-credential transaction is only as reliable as the identity beneath it. If that identity breaks when a card changes, the commercial model breaks with it. Merchants who recognise this move lifecycle management out of the “payments” silo and into the broader retention strategy. Product teams align billing cadence, retry logic and customer experience flows around the stability that network tokens provide.
Treat lifecycle updates as a core revenue asset
The most successful high-risk merchants in 2026 view lifecycle continuity as a predictable revenue driver. When tokens update instantly with issuer-driven changes, recurring billing behaves like a long-lived relationship rather than a series of fragile monthly attempts. Stakeholders across finance, growth, CRM and risk management treat lifecycle KPIs with the same weight they give to churn rate or net revenue retention. Approval stability becomes a measurable input to customer lifetime value, not a back-end detail.
Integrate orchestration, routing and authentication around token behaviour
A token-first strategy also means recognising how lifecycle continuity interacts with the wider payment stack. Orchestration engines route more effectively when credentials behave consistently. Authentication flows are smoother when issuers encounter familiar tokens rather than outdated PANs. Fraud models rely on the stability of identity signals that lifespan-managed tokens naturally maintain. The merchant’s entire infrastructure benefits when every decision is anchored to a credential that the issuer trusts.
Move from “PAN replacement” to “identity management”
The true strategic shift comes from abandoning the legacy mindset of “storing card numbers” and embracing the idea of managing customer payment identities. Tokens with lifecycle management are not static pieces of data; they represent the evolving relationship between the customer and their issuer account. Merchants who adopt identity-centric thinking reshape their architecture: tokens become the central key, and every billing, routing and retry mechanism revolves around them.
The strategic outcome: predictable revenue, predictable retention
A token-first engine produces a rare quality in high-risk payments: predictability. Approval curves stabilise, involuntary churn drops, authentication friction fades and operational overhead falls. What emerges is not merely improved payment performance, but a mature commercial framework where recurring revenue continues without interruption even when cards, devices, routes or issuers change.
In 2026, merchants who build around token lifecycle continuity gain something their competitors cannot replicate quickly: a retention engine rooted in stability, trust and issuer alignment. This is the future foundation of stored-credential commerce.
Conclusion
By 2026, tokenisation will no longer be defined by encryption or PCI scope reduction. The real transformation comes from lifecycle management, the ability for tokens to remain stable and usable even as the underlying card changes. This continuity solves the most persistent structural weakness in digital payments: the fragility of stored credentials. Where PANs expire, break or trigger unnecessary declines, lifecycle-managed tokens continue to function, preserving the customer relationship and the merchant’s revenue stream.
For high-risk merchants, the impact is especially significant. Their portfolios experience higher card turnover, more issuer-driven reissuance and greater volatility across corridors. Token Lifecycle Management neutralises these pressures. Renewals succeed, retries recover, and authentication patterns become more predictable. Instead of firefighting declines, merchants operate with a foundation of consistent identity trusted by issuers and adaptable across routes, PSPs and acquirers.
The broader regulatory environment reinforces this shift. PCI DSS v4.0 encourages merchants to move away from raw PAN handling, while PSD3 emphasises stronger authentication, cleaner risk signals and secure stored credentials. Network tokens, continually refreshed through lifecycle updates, align naturally with these expectations. They support safer authentication, reduce fraud friction and provide issuers with data they interpret as low-risk and stable.
Ultimately, Token Lifecycle Management represents a new model for recurring payments in 2026: a model built not on the customer constantly revalidating their card, but on a persistent payment identity that evolves with them. Merchants who embrace lifecycle continuity gain a structural advantage: higher approvals, lower involuntary churn, smoother authentication and more resilient revenue.
The merchants who delay adoption will increasingly feel the gap. The ones who lead will treat lifecycle-managed tokens not as a backend mechanism, but as a commercial asset and a fundamental engine of long-term customer retention.
FAQs
1. What is Token Lifecycle Management and how is it different from basic tokenisation?
Basic tokenisation replaces PANs with secure tokens, reducing PCI scope. Token Lifecycle Management (TLM) goes further by ensuring those tokens are automatically updated whenever the underlying card changes. This prevents declines caused by expired or reissued PANs and stabilises approval performance. In 2026, TLM is considered essential for merchants relying on stored credentials, subscriptions, wallets and recurring payments.
2. How does TLM improve approval rates for high-risk merchants?
Issuer approvals depend heavily on credential continuity. When merchants continue billing a stale PAN, issuers downgrade risk confidence and decline the transaction. Lifecycle-managed tokens remain aligned with the issuer’s most recent account data, allowing authorisations to pass with fewer false declines. This leads to smoother approval curves in high-risk sectors such as gaming, FX, digital goods and cross-border e-commerce.
3. Does Token Lifecycle Management reduce involuntary churn?
Yes, most involuntary churn is caused by failed renewals triggered by expired or replaced cards. TLM eliminates these failure points by keeping the token active and updated after card reissuance. Subscriptions, SaaS platforms and digital wallet models experience fewer dropped renewals and significantly reduced payment-related churn.
4. Is TLM required under PCI DSS v4.0 or PSD3?
TLM is not mandated by PCI DSS v4.0 or PSD3, but it strongly aligns with both. PCI DSS v4.0 encourages merchants to reduce reliance on raw PANs, while PSD3 supports strong authentication and secure stored credentials. Lifecycle-managed tokens satisfy these expectations by providing a secure, continuously updated identity that issuers trust.
5. How does TLM affect 3DS2 authentication flows?
3DS2 friction is often triggered by inconsistent or outdated credentials. When a PAN no longer matches the issuer’s record, authentication confidence drops and SCA challenges increase. TLM maintains a consistent identity across card changes, enabling smoother frictionless flows and fewer forced step-ups. Merchants see more predictable authentication behaviour, especially for recurring transactions.
6. Can TLM work with multi-acquirer routing and orchestration platforms?
Yes, and this is where lifecycle tokens provide the greatest performance lift. In multi-acquirer setups, a stale PAN produces inconsistent behaviour across different routes. TLM ensures every acquirer receives the same updated credential, stabilising approvals and improving fallback performance. Orchestration engines rely heavily on this stability for accurate routing decisions.
7. What KPIs should merchants track to measure lifecycle performance?
The core KPIs include lifecycle update success rate, token–PAN approval uplift, retry recovery rate, decline-type distribution shift and reduction in involuntary churn. Merchants also track cross-acquirer stability to understand whether credentials behave consistently across routes, a key signal in multi-PSP environments.
8. Does TLM eliminate the need for account updater services?
TLM largely replaces the need for a traditional account updater. Account updater relies on batch updates and issuer participation; lifecycle updates are real-time and network-driven. Merchants still benefit from account updater as a supplementary mechanism, but TLM covers far more reissuance cases and provides higher approval stability.
9. How quickly do lifecycle updates apply after a card is reissued?
Lifecycle updates are typically propagated in real time. Once the issuer reassigns the card details, Visa Token Service (VTS) or Mastercard MDES updates the token mapping instantly. The PSP receives the update immediately, ensuring the merchant’s token remains valid for the next billing attempt.
10. Are lifecycle-managed tokens safer than storing encrypted PANs?
Yes, lifecycle-managed tokens never expose raw card data, significantly reducing the merchant’s PCI compliance burden. They also carry stronger identity signals and are less attractive targets for fraud. Stale PANs stored in vaults can become high-risk credentials; lifecycle-managed tokens maintain alignment with issuer-level security.
11. Which industries benefit most from TLM?
Any merchant relying on stored credentials benefits, but the largest gains are seen in high-churn models: SaaS subscriptions, streaming, gaming, FX, digital wallets and high-frequency services. These verticals experience the highest decline rates from outdated cards, so lifecycle continuity directly improves revenue and retention.




