Card security has always been shaped by one principle: protect the PAN. For nearly two decades, PCI DSS defined how merchants, PSPs and acquirers should encrypt, store and control access to cardholder data. But the payments landscape entering 2026 looks very different from the environment PCI was originally designed for. Fraud has become more automated, issuers deploy increasingly aggressive risk models, and global commerce now depends on multi-acquirer routing, embedded payment stacks and cross-border token mobility. In this world, traditional PCI encryption and PAN vaults continue to provide baseline protection, but they no longer deliver the performance, stability or compliance assurance merchants need.
This shift explains why network tokenisation, once a specialist scheme-led feature, has moved to the centre of issuer strategy and gateway architecture. Unlike PCI vault tokens, which mask a PAN inside a PSP or gateway environment, network tokens are created and maintained by the card networks themselves. They travel through the ecosystem as first-class payment credentials, dynamically updated when an underlying card is reissued and cryptographically bound to devices, merchants or channels. This makes them far more than a security upgrade: they meaningfully reduce false declines, stabilise recurring billing and strengthen authentication outcomes.
Regulatory momentum reinforces this direction. PCI DSS v4.0 tightens scoping rules and pushes organisations to minimise their exposure to raw card data, while the EU’s PSD3 and PSR reforms raise expectations around strong customer authentication, fraud-data reporting and operational resilience. None of these frameworks explicitly mandate network tokenisation, yet the combined effect is clear: regulators, issuers and schemes all expect merchants to adopt credential models that materially lower fraud and reduce their dependency on PAN storage.By 2026, the question facing high-risk merchants is no longer whether network tokens improve security; it is whether operating without them is still commercially or operationally viable. With higher approval rates, lower fraud ratios and better lifecycle continuity, network tokenisation has evolved from a scheme feature into a new compliance and performance baseline across digital commerce.
- From PCI Encryption & Vault Tokens to Network Tokenisation
- How Scheme Tokenisation Works (EMV, Visa, Mastercard)
- Compliance Drivers: PCI DSS v4.0 + PSD3/PSR Expectations
- Merchant Benefit #1: Approval Lift & Fewer False Declines
- Merchant Benefit #2: Fraud-Rate Reduction & Stronger Risk Signalling
- Merchant Benefit #3: Lifecycle Management & Recurring Revenue Stability
- Network Tokenisation + 3DS2: Towards a Stronger Compliance Stack
- Network Tokens in High-Risk & Multi-Acquirer Environments
- Decision Matrix: PAN Storage vs Vault Tokens vs Network Tokens
- Integration Roadmap: Orchestration, API Token Vaulting, Certification
- KPI Framework for Measuring Tokenisation Performance
- Building a 2026 Token-First Merchant Strategy
- Conclusion
- FAQs
From PCI Encryption & Vault Tokens to Network Tokenisation
Card security originally evolved around a simple principle: protect the primary account number. For years, PCI DSS set the global benchmark for how merchants and PSPs should encrypt, store and manage access to cardholder data. Encryption standards improved, vaulting models emerged to reduce exposure, and gateways increasingly offered tokenisation systems that replaced a PAN with an internal token. These vault tokens reduced PCI scope and supported recurring payments, but the underlying challenge remained: the payment ecosystem still relied on transmitting and managing raw PANs in multiple environments.
As digital commerce expanded, this approach began to show its limits. PAN vaulting continued to depend on strong encryption and tight access controls, yet it did nothing to address the operational friction caused by card reissuance, issuer risk filters or inconsistent routing across acquirers. A vault token is ultimately only a reference, it has no intrinsic trust value to an issuer, and it cannot adapt when a customer’s card details change.
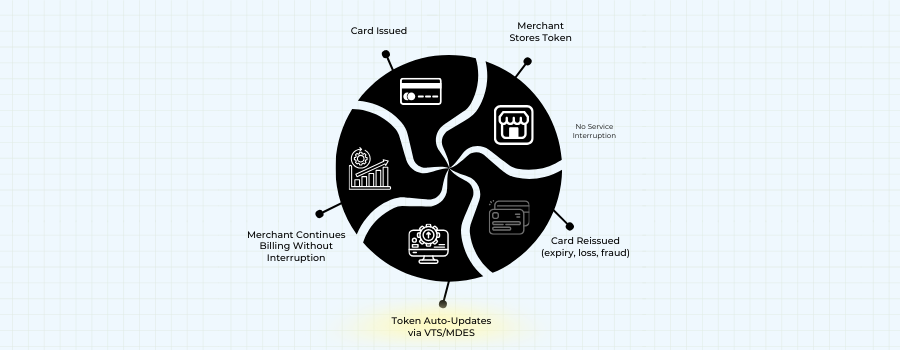
This is the gap that network tokenisation was designed to close. Instead of relying on merchant-controlled replacement tokens, network tokens substitute the PAN at the earliest possible stage and remain valid across the entire lifecycle of the card. Because these tokens are issued and maintained by the card networks themselves, they are cryptographically bound to specific devices, channels or merchant environments. When an underlying card is reissued whether due to expiry, fraud or a portfolio migration the token does not break. The network updates it automatically, allowing merchants to avoid involuntary churn and reducing the frequency of declines.
At the same time, the regulatory environment has shifted toward stronger security expectations for all PSPs and merchants. While PCI DSS v4.0 continues to define how cardholder data must be protected, European regulatory reform under PSD3 and the forthcoming Payment Services Regulation (PSR) brings a renewed focus on fraud reduction, data integrity and operational resilience. The European Commission’s proposal outlines higher supervisory standards and tighter rules on authentication and fraud reporting, reinforcing the industry’s move toward modern credential handling.
Network tokenisation aligns naturally with these expectations. It reduces the number of environments where PANs are ever present, simplifies SCA flows when paired with 3DS2, and provides issuers with more reliable signals about transaction legitimacy. In practice, this means network tokens are no longer just an optional enhancement, they represent a structural change in how card data is handled across the ecosystem.
By 2026, the industry has effectively moved from securing raw card data to eliminating it from merchant systems altogether. PCI encryption and vault tokens remain important elements of the security stack, but network tokenisation sits above them as the more resilient, adaptive and issuer-trusted method. This is the inflection point: the transition from protecting card data to removing card data, and treating network tokens as the default credential for card-not-present commerce.
How Scheme Tokenisation Works (EMV, Visa, Mastercard)
The modern tokenisation ecosystem is built on EMVCo standards, which define how a primary account number can be replaced with a secure payment token that functions as a full-fidelity credential. Unlike gateway vault tokens, which exist only inside the merchant or PSP environment, EMV payment tokens are recognised by issuers, networks and acquirers as legitimate transaction instruments. This makes them structurally different: the token is not merely a placeholder, but a credential with its own lifecycle, cryptographic properties and authentication logic.
At the centre of the ecosystem is the Token Service Provider (TSP), a role fulfilled primarily by Visa and Mastercard. When a PAN is converted into a network token through VTS (Visa Token Service) or MDES (Mastercard Digital Enablement Service), the payment network creates a token that can be bound to a specific device, channel or merchant. This binding makes the transaction environment more predictable for issuers.
A token used consistently through the same merchant or device context carries a lower fraud signal compared with a raw PAN that might appear across multiple channels.
Visa’s token framework emphasises lifecycle continuity, ensuring that when an underlying card is reissued, the token remains active, updated and attached to its original merchant context. Mastercard’s model focuses heavily on domain controls and cryptogram logic, enabling the network to assess whether a token is being used under the correct conditions. In both systems, the TSP continuously monitors token health, manages replacements when cards change, and ensures tokens are used only in authorised channels. This is why network tokens integrate seamlessly into mobile wallets, merchant apps and browser-based environments: the networks maintain a live trust model around each credential.
Another important feature is that scheme tokenisation is compatible with multi-acquirer routing. Because the token is recognised across the network, it can be presented to different acquirers without breaking, unlike a gateway token that is usable only within that gateway’s vault. For merchants operating orchestrated or multi-PSP setups in 2026, this interoperability is one of the strongest commercial arguments for adopting scheme tokens. It allows retries, failover and routing optimisations to occur using a consistent credential, which improves both approval probability and transaction reliability.
The regulatory backdrop also reinforces the importance of this model. While EMVCo itself is not a regulator, its technical standards sit within the broader framework of international payments security expectations. In Europe, forthcoming rules under PSD3 and the Payment Services Regulation, published by the European Commission, emphasise fraud-resistant credentials and improved authentication flows areas where network tokens naturally strengthen compliance and operational resilience.
By 2026, scheme tokenisation has matured into a globally interoperable system backed by billions of provisioned tokens. With EMVCo standards as the foundation and Visa/Mastercard driving wide adoption across issuers and acquirers, network tokens now function as the default architecture for securing card-not-present transactions while improving performance. This marks a major shift: card data is no longer simply protected, it is replaced, maintained and validated through a network-managed identity that is inherently more secure and more predictable than the PAN it substitutes.
Compliance Drivers: PCI DSS v4.0 + PSD3/PSR Expectations
The transition toward network tokenisation is not happening in isolation. It sits directly within the tightening regulatory and security environment shaping global payments from 2024 to 2026. PCI DSS v4.0 raises the baseline for cardholder-data protection, while Europe’s PSD3 and the forthcoming Payment Services Regulation (PSR) push PSPs and merchants toward higher authentication standards, stronger operational controls and deeper fraud reporting. Together, these frameworks create a climate where relying solely on raw PAN storage or internal vault tokens is no longer considered adequate.
PCI DSS v4.0 maintains the long-standing principle that merchants must secure every environment containing primary account numbers. Version 4.0 introduces stricter interpretation of “in-scope” systems, heightened expectations for encryption controls and a new emphasis on continuous monitoring. While the standard does not mandate tokenisation, it explicitly recognises tokenisation as a technique that can remove card data from scope. This means organisations that replace PANs with network tokens reduce their compliance burden, simplify audits and avoid the growing operational cost of maintaining encrypted cardholder-data environments.
PSD3 and the new EU Payment Services Regulation (PSR) move the industry even further. They are designed to strengthen authentication, reduce fraud, increase supervisory oversight and improve the security of remote transactions. These reforms emphasise more consistent SCA outcomes, strengthened fraud-data reporting, and reinforced protection of sensitive credentials. Although PSD3 does not prescribe network tokenisation, it creates an environment where insecure or static credentials are increasingly incompatible with regulatory expectations.
For merchants and PSPs, the combined effect can be summarised through three practical pressures:
- Less tolerance for raw PAN exposure. Any environment where PANs are collected, stored or transmitted automatically attracts heavier compliance oversight under PCI DSS v4.0.
- Higher expectations around authentication quality. PSD3/PSR evaluate the effectiveness of SCA flows, and network tokens naturally support more predictable 3DS outcomes by binding credentials to trusted devices or channels.
- Stronger fraud accountability. Regulators increasingly judge PSPs by measurable fraud outcomes, not just their stated controls. Tokenised transactions often carry lower risk scores at issuer level.
By 2026, the regulatory direction has become clear. PCI DSS remains the global foundation, but its rising scoping requirements and the EU’s emphasis on secure credential handling push the industry toward credential models that eliminate raw card data wherever possible. Network tokenisation fits squarely within this expectation: it is not mandated, yet it aligns perfectly with the security, authentication and fraud-reduction goals embedded in these frameworks.
Merchant Benefit #1: Approval Lift & Fewer False Declines
One of the strongest commercial arguments for network tokenisation in 2026 is its measurable impact on authorisation performance. While traditional PCI vault tokens protect card data, they do not influence how issuers assess risk or authenticate a transaction. A vault token has no inherent “trust signal”; it is simply an internal reference used by the merchant or PSP. Network tokens, by contrast, are part of the scheme-controlled credential infrastructure. This means that when an issuer receives a tokenised transaction, it carries far richer context than a raw PAN ever could.
The improvement begins with lifecycle continuity. A significant share of card-not-present declines come from expired or reissued cards events merchants cannot predict. Network tokenisation addresses this by ensuring that when a card changes, the token does not break. The token remains valid, and the underlying card credentials update automatically. For merchants with recurring billing, stored credentials or in-app wallets, this removes a large proportion of involuntary churn and reduces the silent declines that typically appear as “insufficient funds” or “do not honour” responses.
Equally important is how issuers score tokenised transactions. A PAN entering the ecosystem from multiple channels mobile, browser, recurring billing, or a new device can trigger risk filters because the issuer sees inconsistent usage patterns. Network tokens solve this problem by binding the credential to a specific device, merchant or domain. When that token reappears, issuers recognise it as the same trusted entity. This improves the issuer’s confidence in the transaction, which in turn reduces false declines linked to fraud suspicion or unfamiliar device fingerprints.
Network tokenisation also enhances the authentication journey. Issuers increasingly map device-bound tokens to known customer profiles, making authentication smoother and reducing the frequency of unnecessary 3DS challenges. In environments where frictionless flows depend on issuer trust, network tokens provide the consistency issuers prefer. This becomes especially important in high-risk verticals, where marginal improvements in challenge rates or issuer confidence can translate into meaningful gains in completed transactions.
The combined effect is that tokenised transactions often outperform PAN-based transactions in approval rates, especially for merchants with large subscription volumes, multi-market user bases or high dependence on stored credentials. Network tokens do not guarantee issuer acceptance, but they eliminate many of the structural reasons transactions fail: card reissues, device inconsistencies, fragmented routing and poor risk signals. By 2026, these benefits have made network tokenisation one of the most reliable ways for merchants particularly high-risk merchants to reclaim revenue lost to false declines.
Merchant Benefit #2: Fraud-Rate Reduction & Stronger Risk Signalling
Fraud reduction is often described as a secondary benefit of network tokenisation, but in practice it is one of the strongest drivers of adoption. The core weakness of PAN-based transactions is that the credential is static. Once a PAN is exposed whether through phishing, database compromise or interception, it can be reused across multiple environments, and issuers must rely on behavioural risk scoring to detect misuse. Even with PCI-compliant controls, merchants cannot prevent cardholders from being targeted elsewhere, nor can they influence the way issuers interpret suspicious activity.
Network tokenisation changes this dynamic entirely. Because a network token is cryptographically bound to a specific device, merchant or domain, it becomes extremely difficult for attackers to use it outside its intended context. A token issued for an iOS device cannot be used on an Android emulator; a token generated for a merchant’s mobile app cannot be replayed through a web skimmer; and a token provisioned for a single PSP cannot be exploited across a different route. This binding dramatically increases the cost and complexity of fraudulent attempts, reducing the value of credential theft.
Equally important is the presence of dynamic cryptograms. A tokenised transaction includes a cryptographic value that is unique to that moment and environment, meaning that intercepted data cannot be reused.
Fraudsters who rely on credential replay, one of the most common attack vectors in card-not-present environments gain nothing from obtaining a tokenised transaction payload. The cryptogram becomes invalid the moment it is used, and the token itself is unusable outside its authorised parameters.
For issuers, tokenisation provides a clearer risk signal. When they receive a token, they also receive information about how and where that token has been used historically. Unlike PANs, which travel across multiple channels with no inherent context, tokens develop behavioural fingerprints. This makes issuer fraud models more accurate and significantly reduces false positives. In high-risk verticals where issuer paranoia is high, the difference between a token’s behavioural pattern and a PAN’s ambiguity can determine whether a transaction is approved or declined.
The fraud-reduction effect is amplified in recurring or stored-credential flows. Traditional PAN storage exposes merchants to the risk that a compromised PAN could be used fraudulently on another platform, triggering issuer risk responses that impact legitimate transactions. Network tokens isolate this risk: misuse elsewhere in the ecosystem does not affect the merchant’s tokenised traffic because the token cannot be used cross-channel. This improves the stability of long-term customer relationships and protects subscription portfolios from external fraud events.
By 2026, these mechanisms make network tokenisation one of the most reliable ways to reduce fraud in digital commerce particularly for high-risk merchants facing elevated attack volumes and stricter issuer controls. Fraud losses decrease not just because tokens are harder to exploit, but because issuers inherently trust tokenised credentials more. That trust translates into better authentication outcomes, fewer false declines and a more resilient payments environment overall.
Merchant Benefit #3: Lifecycle Management & Recurring Revenue Stability
In digital commerce, especially where subscription billing or stored credentials dominate, unexpected payment failures can be one of the largest drivers of revenue leakage. Most of these failures are not caused by the customer choosing to cancel; they occur because the underlying card changes and the merchant has no visibility of it. This is where network tokenisation delivers a structural advantage that PCI vault tokens and account updater services have never fully solved.
Lifecycle continuity: The hidden performance engine
When a network token is created, it does not merely mask a PAN; it becomes a living credential managed directly by the card network. Every time a customer’s card is reissued due to expiry, fraud replacement or a bank-wide portfolio migration the network updates the token automatically. This continuity means the merchant never needs to refresh stored details, and the customer experiences no disruption to their billing cycle. Unlike traditional account updater services, which depend on acquirer participation and timing windows, network token lifecycle management operates in real time and applies globally.
Reducing involuntary churn in high-risk verticals
For high-risk merchants, the difference is material. Subscription platforms, gaming wallets, FX services and digital goods merchants often handle large volumes of small-value recurring transactions that are highly sensitive to issuer behaviour. Card reissues can quietly break thousands of stored credentials. Network tokenisation removes this fragility. A token associated with a recurring mandate remains stable even if the underlying card number changes, protecting the merchant from involuntary churn and supporting a more predictable revenue cycle.
Stabilising stored credentials across multi-acquirer environments
Another challenge for high-risk merchants is that stored credentials often move across different acquirers or PSPs depending on routing logic or contingency events. Vault tokens do not travel across providers, which means stored-card flows usually require a single gateway or a complex vault-migration project. Network tokens solve this by being recognised across the ecosystem. When a merchant switches or balances traffic between acquirers, the token behaves consistently, reducing the risk of broken retries or unexpected declines after provider changes.
Protecting revenue from issuer-side risk resets
Issuers continuously update their fraud models, and these changes can unexpectedly introduce new friction or false declines for stored-card traffic. Network tokens soften this volatility. Because the token reflects a known device, known merchant and known usage pattern, issuers view it as a lower-risk credential. When fraud rules tighten, tokenised recurring transactions are far less likely to be caught in broad-brush filters. This protects long-term customer relationships and reduces the operational burden of manual recovery.
By 2026, lifecycle management has become one of the most commercially valuable aspects of network tokenisation. It transforms card credentials from fragile and easily disrupted to stable, network-maintained assets that support predictable recurring revenue. For high-risk merchants, this stability is not a convenience, it is a competitive advantage.
Network Tokenisation + 3DS2: Towards a Stronger Compliance Stack
Strong Customer Authentication has reshaped the way card-not-present payments are authorised, but it also exposed a core weakness in traditional credential handling: issuers often struggle to distinguish legitimate customer behaviour from fraud when the underlying PAN appears across multiple devices, channels and merchant environments. This ambiguity contributes to unnecessary 3DS challenges, friction at checkout and a measurable impact on approval rates. Network tokenisation helps resolve this by aligning credentials with authentication behaviour, giving issuers the context they need to validate identity with greater confidence.
Why tokens and 3DS2 reinforce each other
3DS2 was designed to provide richer data for risk-based authentication, enabling issuers to reduce friction when the risk signal is low. Network tokens enhance this by adding a stable, domain-specific credential into the mix. A token bound to a device or merchant creates a consistent identity footprint, meaning issuers see a familiar, low-risk pattern even when the customer’s device or network environment changes. This reduces the chance of unnecessary challenges and improves the likelihood of a frictionless flow.
Device binding and cryptograms strengthen issuer trust
Each tokenised transaction carries a dynamic cryptogram that reflects the device, channel and moment of use. For issuers, this creates a far more reliable signal than a static PAN ever could. When the same token consistently generates cryptograms within a predictable range of parameters, the issuer’s risk model becomes more accurate. This not only supports better SCA decisions but also reduces the false positives that lead to friction for legitimate customers. The issuer effectively receives both the authentication data from 3DS2 and the credential integrity signal from the token a combination that is rare in PAN-based flows.
Supporting SCA exemptions and lower-friction journeys
European issuers increasingly rely on transaction-risk analysis to grant exemptions under PSD2 and, soon, PSD3. These exemptions depend heavily on the credibility of the risk signal. Network tokens provide a credential that is far harder to spoof or misuse, making issuers more comfortable approving low-risk, low-value or recurring transactions without forcing a challenge. In high-risk commerce, where issuer conservatism can slow down user journeys, even small increases in exemption success rates can translate into significant lift in completed transactions.
Reducing authentication volatility across multi-acquirer setups
In environments where merchants use multiple PSPs or orchestrated routing, inconsistent credential presentation is one of the main reasons authentication and approval rates fluctuate. A PAN routed through two different providers can appear to issuers as two entirely different customers. Network tokens eliminate this inconsistency: regardless of which acquirer handles the transaction, the token identity and its associated history remain constant. This stabilises authentication behaviour, reduces edge-case declines and improves the overall reliability of SCA flows.
By 2026, the integration between network tokenisation and 3DS2 has become a cornerstone of secure digital commerce. Tokens provide the stable identity foundation; 3DS2 supplies the dynamic behavioural data; and together they enable issuers to make faster, more accurate decisions. For merchants, especially those operating in high-risk categories, this alignment is critical. It lowers friction, reduces false declines and creates a more consistent customer experience, not through shortcuts or exemptions, but through stronger, smarter authentication.
Network Tokens in High-Risk & Multi-Acquirer Environments
High-risk merchants operate in markets where approval rates swing quickly and issuer behaviour shifts without warning. This volatility becomes even more pronounced when payments are routed across multiple acquirers, PSPs or orchestration layers. The core weakness is always the same: a raw PAN appearing through different providers looks inconsistent to issuers. Network tokenisation reshapes that dynamic by giving every provider in the routing chain a single, stable identity signal.
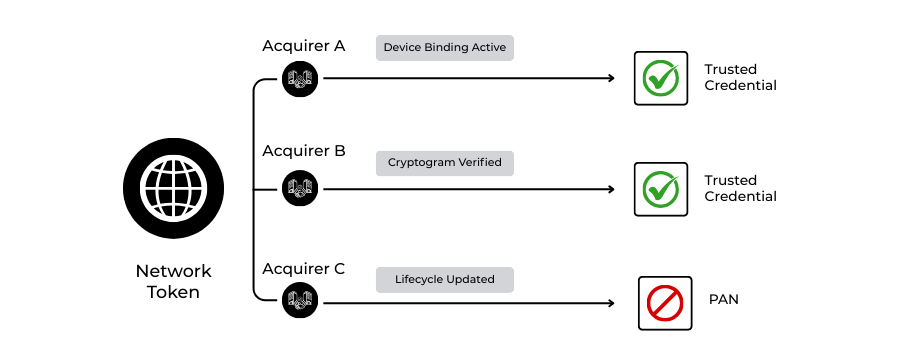
How identity consistency stabilises routing
In a multi-acquirer setup, a PAN processed through one PSP may behave very differently when routed through another, even if the merchant, device and user are identical. Issuers treat each route as a new environment. A network token avoids that fragmentation. Its behavioural history, the device binding, cryptogram characteristics and usage patterns, stays intact no matter which provider presents it. Merchants gain the freedom to route for performance without sacrificing predictability.
The impact during retries and fallback flows
This consistency becomes critical when a payment requires retries. With traditional PAN-based logic, a retry through a second provider often triggers the same decline reason because the credential carries no contextual memory for the issuer. Tokens behave differently. If the issuer has already seen the token in a trusted pattern, a retry is judged with far greater nuance. The issuer sees continuity, not risk escalation, which significantly improves soft-decline recovery in high-risk verticals.
Why tokens matter more in volatile corridors
Corridors such as LATAM, Southeast Asia and parts of Eastern Europe present amplified decline risk due to aggressive issuer controls or historical fraud patterns. In these markets, the consistency of a network token helps issuers separate legitimate merchant behaviour from credential misuse. A token that appears across corridors still retains its same trust signature, something a PAN can never do because it travels everywhere.
A shift from fragile credentials to durable ones
Merchants operating across multiple providers traditionally face a difficult trade-off: optimise routing or preserve credential integrity. Network tokenisation removes this trade-off entirely. The token becomes the stable credential, while the routing logic can change dynamically based on acquirer performance, cost, scheme rules or user geography. This architecture mirrors what the most successful PSPs already do internally, unifying identity while diversifying routing and extending it to merchants.
Network tokenisation, therefore becomes more than a security measure; it becomes a foundational element of a high-risk, multi-acquirer strategy. It creates a predictable identity layer across a fragmented ecosystem, reduces issuer suspicion during provider shifts and supports the routing flexibility modern merchants depend on. By 2026, this stability is indispensable for any merchant that runs orchestration or operates in performance-sensitive verticals.
Decision Matrix: PAN Storage vs Vault Tokens vs Network Tokens
Merchants have spent years relying on PCI encryption and vault tokens to reduce exposure to raw card data, but these methods were never designed to improve issuer trust or routing performance. By 2026, the landscape will have shifted. PAN storage, gateway tokens and network tokenisation each offer a fundamentally different security posture and operational outcome. The matrix below captures the key contrasts that determine how merchants structure their credential strategies today.
Credential Method Comparison Matrix (2026)
| Capability / Risk Area | PAN Storage (Encrypted) | Vault Tokens (Gateway/PSP) | Network Tokens (Visa/MC) |
| PCI Scope | Highest | Reduced | Lowest (PAN removed entirely) |
| Issuer Trust Signal | Weak | None | Strong (device/domain-bound) |
| Fraud Resistance | Moderate | Moderate | High (dynamic cryptograms) |
| Lifecycle Management | Manual / card-updater | Partial | Automatic, real-time |
| Multi-Acquirer Compatibility | Low | Very low | High (ecosystem-wide) |
| Approval Rate Impact | Neutral | Neutral | Positive (2–4% uplift typical) |
| Recurring Billing Stability | Low | Medium | High |
| Risk of Credential Replay | High | Medium | Very low |
| Implementation Burden | High | Medium | Medium (PSP/TSP-integrated) |
Interpreting the Differences
PAN storage: secure, but structurally limited
Even with modern encryption, storing PANs keeps the merchant deep inside PCI scope. Issuers see no additional trust value in encrypted PANs, and recurring credentials remain fragile when cards change. PAN storage is now largely the method of last resort rather than best practice.
Vault tokens: a step forward, but only inside one ecosystem
Gateway or PSP tokens reduce compliance scope and simplify internal flows, but their fundamental limitation is clear: they do not travel across providers. A merchant who uses orchestration, retries or multi-acquirer routing quickly hits the boundaries of this model. Vault tokens add security but do not materially improve authentication or approval logic.
Network tokens: the new structural baseline
By replacing the PAN at the network level, EMV tokens become portable, issuer-trusted credentials with lifecycle continuity baked in. They outperform vault tokens in fraud resistance, approval rates and stability across routes, making them the credentials merchants increasingly depend on in 2026. For PSPs and high-risk merchants, this model is not a “nice to have” but the foundation of a modern acquisition stack.
Integration Roadmap: Orchestration, API Token Vaulting, Certification
Integrating network tokenisation is not a single technical task; it is a structured programme that reshapes how a merchant or PSP handles card data, routes transactions and manages compliance. By 2026, most large PSPs will already act as token requestors through Visa and Mastercard, while merchants adopt tokenisation either directly or via their orchestration platform. The roadmap below outlines how modern organisations execute this transition without disrupting live payment flows.
Phase 1: Architecture Alignment and Token Requestor Enablement
A successful token strategy begins with clarifying how tokens will enter the stack.
For most merchants, the simplest path is adopting tokens through their PSP or orchestration provider, which already maintains certification with the networks.
Larger platforms may choose to become token requestors themselves, enabling direct provisioning and management of network tokens.
This requires alignment with EMVCo tokenisation specifications, endpoint hardening, and an understanding of how device binding and domain controls will map onto existing payment journeys. At this stage, the goal is to define the token lifecycle: where tokens are created, how they travel through the system and which components will remain in PCI scope.
Phase 2: Replacing PAN Vaults with Token Vaulting and Updating Routing Logic
Once the token entry path is established, the next step is shifting from traditional PAN vaults to token-based vaults. This transition involves migrating stored credentials into token equivalents, ensuring that existing customer profiles continue to function without service disruption. API changes at this stage introduce token provisioning calls, token lookup endpoints and mechanisms for retrieving updated credentials when issuers reissue underlying cards. Orchestration plays a central role: routing engines must be updated so retries, failover and corridor-based routing all rely on network tokens rather than raw PANs. This is where merchants begin to see operational improvement, stored credentials become portable across providers, and routing flexibility no longer breaks recurring payments.
Phase 3: Certification, Testing and End-to-End Fraud/SCA Alignment
The final stage focuses on trust: ensuring that the end-to-end flow behaves consistently across issuers, acquirers and authentication systems. PSPs and merchants must complete scheme certification or confirmation that their integration aligns with Visa Token Service (VTS) and Mastercard MDES requirements. Testing involves verifying that cryptograms are generated correctly, that lifecycle updates are applied in real time, and that tokens flow cleanly through 3DS2 authentication. Additional work is required to align fraud controls; network tokens bring stronger signals, but fraud engines must be recalibrated to interpret them correctly. Once the ecosystem is stable, the merchant gains the full benefit of tokenisation: portable credentials, reduced PCI exposure, higher approval rates and stronger issuer trust.
In 2026, this roadmap will have become a standard practice for PSPs and high-risk merchants transitioning from PCI-bound card storage to token-first infrastructure. The process is structured, predictable and increasingly supported by acquirers and orchestration platforms, making network tokenisation not only a compliance improvement but an operational upgrade.
KPI Framework for Measuring Tokenisation Performance
The value of network tokenisation becomes visible only when merchants track the right indicators. Because tokens influence issuer trust, routing consistency, lifecycle stability and SCA outcomes, the KPI set for 2026 looks different from traditional approval-rate reporting. High-risk merchants, in particular, rely on a focused performance framework to understand where tokenisation is delivering uplift and where further optimisation is needed.
Approval Rate Differential (Token vs PAN)
The core metric is the performance gap between tokenised transactions and PAN-based ones. Measured correctly, this does not reflect the overall approval rate, but rather the uplift generated by replacing raw card data with network-managed credentials. Even a small percentage difference indicates stronger issuer confidence, better authentication patterns and more predictable cross-provider routing.
Lifecycle Update Success Ratio
This KPI measures how often token lifecycle management prevents a decline caused by an expired, replaced or reissued card. For subscription, wallet and stored-credential merchants, a strong lifecycle update ratio signals reduced involuntary churn. It also indicates that the tokenisation implementation is aligned correctly with VTS and MDES update flows.
Soft Decline Recovery Rate
Tokens influence retry behaviour because issuers interpret tokenised retries with more context than PAN-based ones. The recovery rate, therefore becomes a proxy for the health of multi-acquirer routing and authentication consistency. Rising recovery percentages usually correspond to a reduction in issuer-side friction, especially in high-risk corridors.
SCA Challenge Reduction Rate
A key benefit of network tokenisation is more predictable authentication. This KPI measures how much 3DS2 friction has been reduced after token adoption. Lower challenge volumes, combined with steady approval rates, signal that issuers trust the identity footprint created by tokens as an essential measure in regions operating under PSD2 and, soon, PSD3.
Fraud Ratio Shift (Token vs Non-Token)
Fraud ratios are not only a security metric; they influence issuer behaviour directly. When tokenised transactions exhibit lower fraud incidence, issuers begin to treat the merchant’s traffic as structurally lower-risk. This metric also reveals whether fraud systems have been recalibrated to properly interpret token signals.
Cross-Acquirer Consistency Index
Tokens are designed to behave predictably across PSPs. This KPI measures how stable approval rates remain when traffic moves between acquirers. If token performance remains consistent across routes while PAN-based performance fluctuates, the stack is benefiting from issuer-trusted credentials and routing independence.
Retry Path Efficiency
Finally, merchants evaluate how efficiently retries succeed compared to pre-tokenisation benchmarks. Because tokenised retries carry device binding and cryptogram signatures, issuers can differentiate legitimate attempts from risky patterns. A rising efficiency score reflects healthier issuer scoring and cleaner routing logic.
In 2026, these KPIs form the backbone of token-performance reporting. They allow merchants and PSPs to move beyond abstract security benefits and measure network tokenisation in concrete terms: approval stability, authentication quality, fraud resistance and routing resilience. When tracked together, these metrics reveal the full operational and commercial value of replacing PANs with network-managed credentials.
Building a 2026 Token-First Merchant Strategy
A token-first strategy is not simply a technical upgrade; it represents a shift in how merchants manage identity, risk, routing and long-term customer value. By 2026, high-risk merchants that treat tokenisation as part of their core payments architecture outperform those who adopt it only for PCI reduction. A successful strategy requires aligning commercial priorities, issuer expectations and operational design into a single, coherent plan.
Re-framing the role of credentials in the payments stack
Most merchants still view card credentials as a passive input: something stored, retrieved and used during checkout or billing. Network tokenisation reframes the credential as a dynamic, network-maintained identity asset that influences issuer decisions. This means merchants must elevate tokenisation from a compliance task to a performance lever. When routing, retry logic, fraud controls and authentication journeys are built around token identity rather than raw card data, the entire payments stack behaves more consistently.
Embedding tokens into the orchestration layer
Orchestration becomes the foundation of a token-first approach. By ensuring that network tokens are used across every acquirer and every route, merchants eliminate the volatility that arises when PANs appear inconsistently through different PSPs. The orchestration layer must be configured to prioritise tokenised traffic, maintain token continuity during provider switches and ensure that failover routes support cryptogram generation and lifecycle updates. In high-risk commerce, this alignment becomes essential for stabilising approval performance across corridors.
Aligning fraud and SCA systems with token signals
Tokens bring stronger, more interpretable signals to issuer fraud engines, but merchants gain the full benefit only when their own systems are calibrated to recognise and amplify these signals. Fraud models that differentiate between tokenised and non-tokenised traffic allow merchants to reduce unnecessary friction without increasing risk. Similarly, SCA flows should be designed to take advantage of the smoother authentication journey that tokens enable, ensuring frictionless requests are sent whenever issuer risk scores are favourable.
Designing for lifecycle continuity
A token-first approach requires that recurring billing, stored credentials and subscription logic be re-built around lifecycle updates rather than Card-on-File changes. When a card is reissued, the system should rely on token refresh events rather than customer prompts or failed retries. This shift removes one of the largest sources of involuntary churn and supports revenue continuity, especially important in high-risk and high-frequency billing environments where even small disruptions can lead to drop-off.
Creating issuer-friendly identity patterns
Issuers increasingly rely on behavioural consistency to determine risk. A token-first merchant strategy must therefore aim to create predictable token behaviour across devices, channels and providers. Smooth recurring patterns, stable device associations and consistent cryptogram profiles all reinforce issuer confidence. Over time, this trust becomes a competitive advantage, reducing unnecessary declines and improving authentication outcomes across markets.
By treating network tokens as the centre of the payments identity layer, merchants position themselves for stronger approval rates, predictable recurring revenue and a lower overall risk profile. In 2026, this shift is no longer optional for high-risk merchants; it is the strategic foundation that separates resilient payment operations from those still struggling with issuer volatility and credential fragility.
Conclusion
By 2026, network tokenisation will have evolved from a technical enhancement into a structural requirement for merchants that depend on stable approval rates, predictable recurring revenue and issuer-trusted authentication. While PCI DSS v4.0 remains the baseline for securing cardholder data, it no longer defines competitive performance. The shift now comes from replacing static PANs and isolated vault tokens with scheme-managed credentials that carry identity, lifecycle and behavioural continuity across every acquirer and every device.
High-risk merchants feel this shift most sharply. They operate in corridors where issuer risk appetite fluctuates, fraud pressure is high, and routing strategies depend on multiple PSPs. In that environment, network tokens provide consistency where PANs introduce ambiguity. The result is a more resilient checkout, smoother authentication flows, stronger soft-decline recovery and a tangible reduction in involuntary churn. Tokenisation, in other words, restores predictability to systems designed for constant change.
At the same time, the regulatory climate reinforces the transition. PSD3 and the EU’s new payment rules prioritise secure credentials, cleaner authentication and lower fraud tolerance. Network tokenisation fits naturally within that direction of travel and increasingly defines the architecture PSPs, acquirers and orchestration platforms expect from merchants in 2026 and beyond.
The shift is not purely technical; it is strategic. Merchants who treat network tokenisation as a performance layer rather than a compliance add-on unlock the full advantage of issuer trust. Those who do not risk carrying legacy credential models into a world that has already moved on. The merchants who succeed are those who adopt a token-first mindset: routing intelligently, authenticating intelligently and building long-term payment infrastructure around stable, network-managed identities.
FAQs
1. What is the difference between vault tokenisation and network tokenisation?
Vault tokenisation replaces the PAN with a surrogate value generated by a gateway or PSP. It reduces PCI exposure but does not influence issuer trust or approval rates. Network tokenisation, however, replaces the PAN at the scheme level (Visa, Mastercard) and includes device binding, lifecycle updates and cryptographic authentication. Issuers see network tokens as higher-integrity credentials, which results in stronger approval performance and lower fraud. In 2026, vault tokens help with compliance, but network tokens help with both compliance and commercial performance.
2. Do network tokens remove the need for PCI DSS compliance?
No. PCI DSS v4.0 still applies to any system that handles PANs before tokenisation. However, network tokenisation dramatically reduces PCI scope because merchants no longer store or process raw card numbers. It minimises the number of systems exposed to cardholder data and reduces the operational burden of audits, encryption controls and monitoring. PCI obligations do not disappear, but they become easier to satisfy and significantly cheaper to maintain.
3. Will network tokenisation improve approval rates for all merchants?
Not uniformly, but most merchants, especially high-risk and cross-border segments, see a positive uplift. This is because network tokens provide issuers with trusted context: stable lifecycle behaviour, consistent device associations and cryptographic proof of authenticity. PAN-based traffic does not have these attributes, which often leads to unnecessary declines. Improvement is strongest for recurring billing, stored credentials, wallets and multi-acquirer routing environments.
4. Is tokenisation mandatory under PSD3 or the new EU Payment Services Regulation?
No, PSD3 and PSR do not explicitly mandate tokenisation. However, they emphasise secure credential handling, stronger authentication and clearer fraud accountability. Network tokenisation aligns naturally with these objectives because it reduces credential misuse and improves risk-based SCA outcomes. Regulators are not enforcing tokenisation directly, but issuer behaviour and compliance expectations are indirectly pushing merchants toward token-first architectures.
5. How do network tokens support stronger 3DS2 authentication flows?
3DS2 relies on behavioural and device data to support frictionless authentication. Network tokens reinforce these signals by embedding device binding and generating dynamic cryptograms that reflect the transaction’s environment. When issuers receive this combination of 3DS2 data and token identity, they can make more confident decisions, which reduces unnecessary challenges and improves frictionless rates.
6. Can network tokens be used across multiple PSPs and acquirers?
Yes. This is one of their strongest advantages. Because they originate from the card networks, network tokens are recognised across the ecosystem, regardless of which PSP processes the transaction. This portability is critical for merchants using orchestration or multi-acquirer routing. Vault tokens, in contrast, are proprietary and cannot travel across PSPs without migration efforts.
7. What is the impact of network tokenisation on fraud rates?
Tokenised transactions carry far stronger anti-fraud properties: device binding, domain controls and dynamic cryptograms. These make credential replay significantly more difficult. Issuers also trust tokenised behaviour more, which means fewer false positives and tighter fraud modelling. High-risk merchants often see reduced fraud pressure and fewer issuer-driven blocks after migrating to tokens.
8. Do network tokens help reduce involuntary churn in subscriptions?
Yes. Token lifecycle management ensures that when a card is reissued, due to expiry, loss or fraud, the token stays valid and updates automatically. This prevents the silent declines that commonly break subscription billing or stored-credential payments. Merchants that depend on recurring revenue typically see lower involuntary churn and fewer customer interruptions after adopting tokens.
9. Is network tokenisation difficult to integrate for high-risk merchants?
Not anymore. Most PSPs and orchestration platforms already support network tokens through Visa Token Service (VTS) and Mastercard MDES. Integration focuses on updating vault logic, routing paths and API calls rather than rebuilding the entire payments stack. Certification requirements exist for token requestors, but merchants using PSP-managed tokenisation avoid most of this complexity.
10. Will network tokens replace PANs completely in digital commerce?
Not entirely, but they will become the default credential for card-not-present transactions. PANs will still exist for physical cards, fallback scenarios and non-tokenised merchants. However, in high-risk and multi-acquirer digital environments, tokens increasingly become the standard because they reduce fraud, improve approval rates and stabilise routing behaviour.
11. How do tokens impact acquirer and issuer risk models?
Issuers score tokenised transactions differently because they recognise the token, the device and the usage pattern. Over time, this consistency creates a trust profile that reduces false declines. Acquirers also benefit from cleaner routing data and fewer ambiguous risk signals. The net effect is a more predictable authorisation environment with fewer swings caused by issuer behaviour.




