For years, approval rates were treated almost exclusively as a merchant-side problem. If transactions were failing, the assumption was simple: something needed fixing at the checkout UI, or the customer had insufficient funds. In 2026, that view no longer holds. Approval performance is now understood to be a complex ecosystem outcome, shaped just as much by issuer behaviour, card scheme rules, and broader network health as it is by how a merchant configures their payments.
This shift matters because the levers that influence approvals increasingly sit across organisational boundaries. Critical factors such as retry behaviour, authentication decisions, credential quality (like Network Tokens), and routing logic all affect how issuers interpret risk, yet no single party controls them end-to-end. Merchants see declines without context, often interpreting them as lost revenue. PSPs see patterns without product insight, often interpreting them as risk. Optimisation attempts made in isolation often cancel each other out, merchants pushing for more retries while PSPs tighten risk filters.As a result, approval rates have become a shared outcome rather than a simple processor metric. Improving them now depends entirely on how closely PSPs and merchants collaborate on how transactions behave, not just where they are routed. In 2026, the strongest approval gains are coming from aligned operating models that balance conversion, fraud risk, and network expectations, rather than from isolated tweaks or short-term workarounds.
- What Approval Rate Optimisation Actually Means in 2026
- Why Approval Rates Are Harder to Improve Than They Appear
- Where PSP-Merchant Collaboration Historically Breaks Down
- The 2026 Collaboration Model: A Shared Approval Stack
- How High-Performing PSP–Merchant Teams Are Improving Approvals
- Scheme Rules and Network Health: The New Guardrails on Optimisation
- Merchant Checklist: Are You Set Up for Collaborative Approval Gains?
- Conclusion
- FAQs
What Approval Rate Optimisation Actually Means in 2026
Approval rate optimisation in 2026 is no longer about forcing more transactions through the system regardless of quality. It is about shaping payment behaviour so that issuers, schemes, and risk engines remain confident in the merchant’s traffic over time. A short-term lift achieved through aggressive retries or blanket rule changes often creates longer-term damage that is harder to unwind.
For merchants, approvals now sit at the delicate intersection of conversion and sustainability. An approved transaction only has value if it does not trigger downstream consequences: higher fraud exposure, stricter authentication challenges (step-ups), or scheme scrutiny that reduces future performance. This is why optimisation has shifted away from isolated tactics and toward consistency.
A key distinction that many teams still miss is the difference between soft and hard declines:
- Soft Declines (e.g., Insufficient Funds, Do Not Honor): Signal temporary caution or a fixable issue. These can often be recovered with the right next action, such as a targeted retry or a prompt for a different card.
- Hard Declines (e.g., Stolen Card, Invalid Account): Represent a firm refusal. Treating both the same, by retrying blindly or escalating authentication unnecessarily, trains issuers to distrust future attempts from that merchant ID (MID).
In practice, modern optimisation is about reducing noise. Clean data (bolstered by ISO 20022 standards), predictable retry behaviour, and aligned authentication decisions make transactions easier for issuers to approve. The goal is not to maximise approvals at any cost, but to maintain a pattern of behaviour that issuers are comfortable supporting at scale.
In 2026, approval rate optimisation is best understood as managing five interdependent signals:
- Decline quality and interpretation: Knowing exactly what a specific issuer code means in the context of new scheme rules.
- Network-compliant retry behaviour: Ensuring retries happen only when permitted and effective.
- Authentication decisions aligned to risk: Using 3DS and exemptions strategically rather than uniformly.
- Credential quality: Leveraging Network Tokens and Click to Pay (SRC) to refresh card data automatically.
- Routing resilience without masking issues: Using orchestration to solve outages, not to hide bad traffic.
Why Approval Rates Are Harder to Improve Than They Appear
On the surface, approval rates look like a technical metric. A transaction is either approved or declined, and the instinct is to assume there must be a direct technical fix. In practice, issuers do not evaluate transactions in isolation. They evaluate behaviour over time.
Every payment attempt contributes to a broader pattern. How often retries occur, how authentication is applied, how credentials change, and how routing shifts all feed into an issuer’s internal confidence model. When that behaviour feels inconsistent or overly aggressive, such as a merchant suddenly retrying declined transactions 10 times in an hour, issuers respond cautiously even if the individual transactions look legitimate.
This is why approval rates often deteriorate after well-intentioned optimisation efforts. Teams introduce new retry logic, change authentication thresholds, or add routing rules without seeing how those changes interact. The result is a noisier payment profile, not a cleaner one. Issuers see uncertainty, and in the world of payments, uncertainty triggers declines.
The challenge is compounded by feedback delays. The impact of a poor optimisation decision is rarely immediate. Approval rates may hold steady for weeks before sliding as issuer models adjust to the new pattern, making it difficult to trace cause and effect. By the time the issue is visible, trust has already eroded.
In 2026, improving approval rates requires accepting that performance is cumulative. It is shaped by consistency, restraint, and alignment across systems. The hardest part is not knowing what to change, but knowing what not to touch without coordination.
Where PSP-Merchant Collaboration Historically Breaks Down
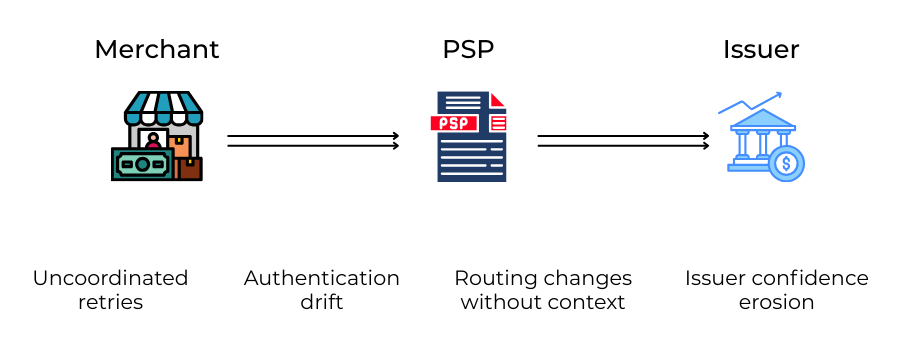
Most approval rate problems do not stem from a lack of effort. They stem from misalignment. Merchants and PSPs are often working hard on the same issue, but from opposite sides of the system, with different incentives and incomplete information.
Merchants optimise for conversion; PSPs optimise for exposure
Merchants experience declines as lost revenue and disrupted customer journeys. The natural response is to push harder: more retries, fewer 3DS challenges, faster routing changes. PSPs, however, sit closer to scheme rules and issuer feedback. When patterns begin to look risky or noisy, their instinct is to slow things down to protect the MID’s standing. Without alignment, one side accelerates while the other applies the brakes.
Merchants lack issuer visibility; PSPs lack product context
Merchants see what happens at checkout and in their OMS (Order Management System). PSPs see aggregate patterns across many merchants. What neither side sees alone is the full picture. PSPs may tighten controls without understanding a product change (like a flash sale) that altered traffic quality. Merchants may change flows without realising how issuers are reacting to similar behaviour elsewhere in the market.
Retry logic becomes harmful without shared governance
Retries are a common flashpoint. Used carefully, they can recover soft declines and save a sale. Used indiscriminately, they create patterns issuers distrust. Without shared rules on timing, limits, and decline handling, retries quickly become counterproductive, looking less like persistence and more like a brute-force attack.
When collaboration breaks down, the same signals tend to appear:
- Authentication rules change independently of retry behaviour (e.g., retrying a 3DS failure without 3DS).
- Retry volumes grow without clear caps or timing discipline.
- Transaction metadata (like MCC codes or descriptors) lacks consistency or context.
- Dispute and fraud feedback is not looped back into the approval strategy.
None of these issues is dramatic on its own. Together, they create the conditions where approval rates quietly deteriorate despite everyone’s best intentions.
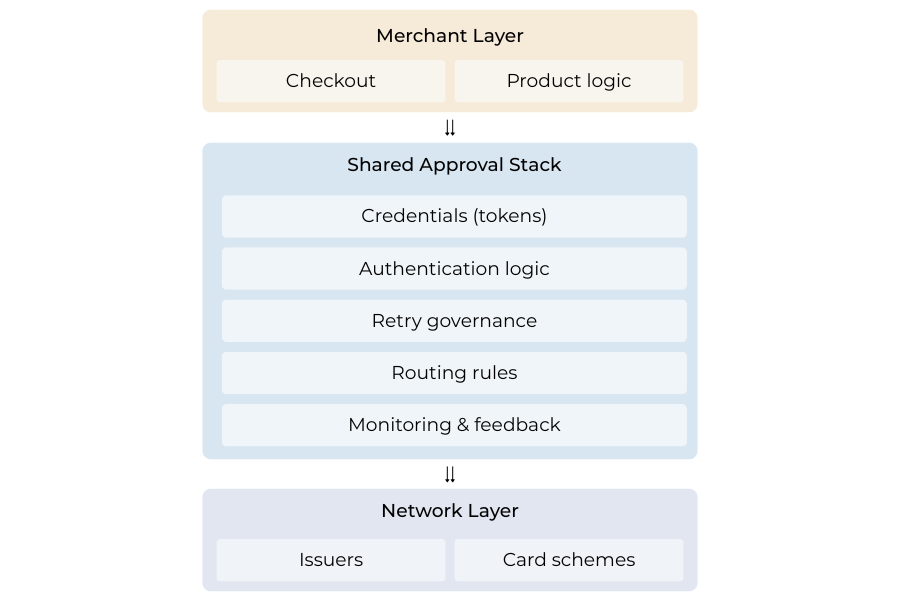
The 2026 Collaboration Model: A Shared Approval Stack
In 2026, the most effective approval improvements are coming from teams that no longer treat optimisation as a series of isolated tweaks. Instead, they are building and governing what can be thought of as a Shared Approval Stack: a set of coordinated controls that shape how transactions behave end-to-end.
This stack is not owned by the merchant or the PSP alone. It sits between them. Routing decisions, credential formats, authentication rules, retry behaviour, and monitoring all interact within this layer. When these elements are adjusted independently, behaviour becomes unpredictable. When they are governed together, patterns stabilise and issuer confidence improves.
What makes this model different is its focus on behaviour rather than tooling. Collaboration is not about adding more features or switching providers. It is about agreeing on how transactions should respond under different conditions and ensuring those responses are consistent. A soft decline triggers a defined next step. A credential change follows a known path (like a Network Token refresh). Authentication is applied deliberately, not reflexively.
By treating approval performance as a system rather than a metric, merchants and PSPs reduce noise across the network. Issuers see fewer contradictory signals, and approvals become easier to sustain. In 2026, this shared approval stack is increasingly the foundation on which reliable payment performance is built.
How High-Performing PSP–Merchant Teams Are Improving Approvals
Teams that are consistently improving approval rates in 2026 share a common approach: they treat optimisation as an ongoing operating discipline rather than a one-off project. The focus is not on chasing marginal gains, but on removing behaviours that quietly degrade issuer confidence.
Treating tokenisation as a performance lever
Tokenisation is no longer viewed only as a security or compliance requirement. High-performing teams use Network Tokens to stabilise credentials over time. Tokens reduce disruption when cards are reissued and provide issuers with cleaner, more recognisable signals. When both PSP and merchant align on token coverage and fallback logic (switching to PAN if the token fails), approval performance becomes more resilient, particularly for stored credentials and repeat transactions.
Governing retries as a network-compliance issue
Retries are handled with restraint. Rather than retrying everything, teams agree on which decline types are recoverable, how long to wait, and how many attempts are acceptable. This prevents retry behaviour from drifting into patterns that issuers interpret as aggressive or abusive, ensuring the merchant stays off scheme excessive retry monitoring programs.
Tuning authentication together instead of defaulting to blanket controls
Instead of switching 3DS on everywhere, merchants and PSPs review where authentication genuinely improves outcomes. Decisions are based on decline patterns, fraud exposure, and customer friction, not fear of chargebacks alone. With Data-Only authentication fields now standard, merchants can pass risk data to issuers without always challenging the user.
Using routing to improve resilience, not to mask problems
Routing is used to manage genuine infrastructure issues, not to hide poor data quality or risky behaviour. Changes are deliberate and reviewed, not left to accumulate unnoticed. Smart routing logic is now issuer-aware, sending transactions to the acquirer most likely to succeed with that specific bank.
- Agreed decline-code interpretation and next actions.
- Defined retry caps and timing rules.
- Tokenisation targets for relevant flows.
- Change control for payment logic updates.
Scheme Rules and Network Health: The New Guardrails on Optimisation
In 2026, approval rate optimisation operates within clearer and tighter guardrails than ever before. Card schemes (Visa, Mastercard, etc.) are no longer passive infrastructure providers. They actively define what acceptable optimisation behaviour looks like, particularly around retries, fraud handling, and transaction integrity.
This shift matters because PSPs are obligated to enforce scheme standards, even when doing so constrains short-term performance. Excessive retries, inconsistent authentication, or patterns that resemble transaction spam are now treated as network health risks. When these signals appear, issuers respond defensively, and schemes expect PSPs to intervene.
For merchants, this can feel like optimisation is being blocked. In reality, it is being bound. Schemes are not preventing approval improvement; they are preventing behaviour that degrades the ecosystem for everyone. PSPs sit in the middle, translating scheme expectations into operational controls that merchants must work within.
This is why collaboration has become essential. When merchants understand the constraints PSPs are operating under, optimisation efforts become more disciplined. Instead of pushing for exceptions or workarounds, teams focus on reducing noise, improving data quality (via ISO 20022 fields), and aligning behaviour with what issuers are willing to trust. In 2026, sustainable approval gains come from respecting network health. Optimisation that ignores these guardrails may produce temporary lifts, but it rarely survives scrutiny.
Merchant Checklist: Are You Set Up for Collaborative Approval Gains?
This checklist is not about tactics. It is a quick way to assess whether your approval optimisation efforts are structurally aligned with how PSPs and schemes expect payments to behave in 2026.
- Declines are categorised and acted on consistently: Soft and hard declines are clearly distinguished, with agreed next actions rather than blanket retries.
- Retry behaviour is governed, not reactive: Timing, frequency, and limits are defined jointly with your PSP and reviewed against issuer response patterns.
- Credential strategy supports continuity: Network Tokenisation or equivalent mechanisms are in place where stored credentials or repeat payments matter.
- Authentication decisions consider performance as well as risk: Step-ups (3DS) are applied deliberately, based on data, not as a default response to uncertainty.
- Payment changes are controlled and reviewed: Routing, rules, and logic updates follow a documented change process rather than drifting over time.
If most of these conditions are met, approval optimisation is treated as a collaborative system, not a series of isolated fixes.
Conclusion
Approval rates in 2026 are no longer something merchants can optimise in isolation or PSPs can solve through tooling alone. They are the outcome of how well both sides align on behaviour, discipline, and shared understanding of risk. When optimisation efforts are fragmented, issuers see inconsistency and respond cautiously. When they are coordinated, approval performance stabilises.
The shift toward collaboration reflects a broader reality in payments. Issuers and schemes increasingly reward predictability, clean signals, and restraint. PSPs are required to enforce those expectations, and merchants who understand that context are better positioned to improve performance without triggering unintended consequences.The strongest approval gains now come from treating payments as a governed system rather than a collection of levers. Shared decline interpretation, controlled retries, aligned authentication, and disciplined change management reduce noise across the network. In 2026, approval optimisation is no longer about pushing harder. It is about working together to make transactions easier for issuers to trust.
FAQs
1. Why can’t merchants improve approval rates on their own anymore?
Because issuers and card schemes now evaluate payment behaviour over time, not just individual transactions. Many of the levers that influence issuer trust retries, authentication patterns, credential quality, and routing behaviour sit partially or entirely with PSPs. Optimising in isolation often creates conflicting signals that reduce approvals rather than improve them.
2. What does it mean to say approval rates are an ecosystem outcome?
It means approvals are shaped by how merchants, PSPs, issuers, and schemes interact collectively. Even a well-configured checkout can suffer if retry behaviour, authentication decisions, or routing patterns degrade network confidence over time.
3. Why do aggressive retries often make approval rates worse?
Because issuers interpret excessive or poorly timed retries as noise or hostile behaviour. While a single retry might recover a soft decline, repeated attempts without clear justification train issuers to distrust future transactions from the same merchant ID.
4. What’s the practical difference between soft and hard declines?
Soft declines indicate temporary caution and may be recoverable with the right next step. Hard declines represent firm refusals. Treating both the same by retrying blindly or escalating authentication unnecessarily damages issuer trust and long-term approval performance.
5. How does tokenisation actually help approval rates?
Network tokens stabilise credentials over time, especially when cards are reissued or expire. This reduces disruption, improves issuer recognition, and leads to more consistent approvals for stored and repeat transactions when merchants and PSPs align on token usage.
6. Why is blanket 3DS enforcement no longer effective?
Because unnecessary authentication introduces friction without always improving issuer confidence. In 2026, high-performing teams apply authentication selectively, based on risk, decline patterns, and transaction context rather than fear-driven defaults.
7. Why do scheme rules matter so much for approval optimisation now?
Card schemes actively enforce standards around retries, fraud handling, and transaction integrity. PSPs are required to uphold these rules, which means optimisation must operate within defined guardrails rather than relying on workarounds.
8. How can collaboration actually improve issuer trust?
When merchants and PSPs align on decline interpretation, retry limits, authentication strategy, and data quality, issuers see fewer contradictory signals. That consistency makes transactions easier to approve over time.
9. What are the warning signs that approval optimisation is becoming counterproductive?
Rising retries without clear recovery, inconsistent authentication behaviour, unexplained approval drops weeks after changes, and increasing scheme scrutiny are all signs that optimisation efforts are adding noise rather than clarity.
10. Is routing across multiple PSPs always beneficial for approvals?
No. Routing improves resilience when used deliberately, but it can mask deeper issues if used to bypass declines without addressing data quality, retry behaviour, or risk signals that issuers care about.
11. What’s the biggest mindset shift merchants need to make in 2026?
To stop treating approval rates as something to push higher and start treating them as something to earn through disciplined, explainable payment behaviour that issuers and networks are comfortable supporting.




